September Snafus: Hackers Take Advantage of Unwitting Employees
Approachable Cyber Threats
SEPTEMBER 24, 2022
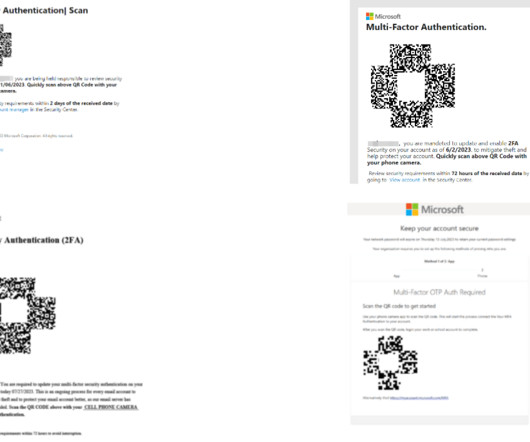
Category News, Social Engineering. All of the attacks were carried out with relatively simple phishing and social engineering techniques. The couple claimed that they were able to trick an employee into downloading malware from a phishing email. Risk Level. The common theme? Phishing and poor password practices.

















Let's personalize your content