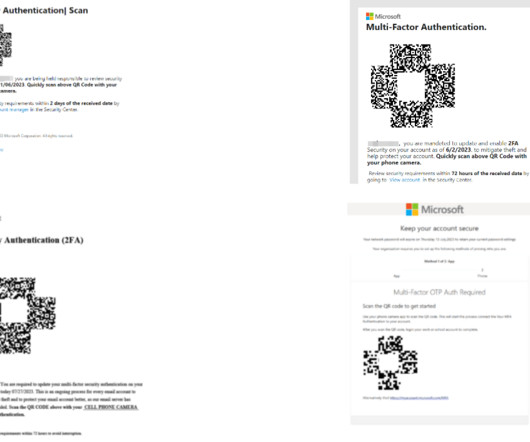
Taking on the Next Generation of Phishing Scams
Google Security
MAY 11, 2022
Posted by Daniel Margolis, Software Engineer, Google Account Security Team Every year, security technologies improve: browsers get better , encryption becomes ubiquitous on the Web , authentication becomes stronger. But phishing persistently remains a threat (as shown by a recent phishing attack on the U.S.
























Let's personalize your content