FIFA 22 phishers tackle customer support with social engineering
Malwarebytes
JANUARY 12, 2022
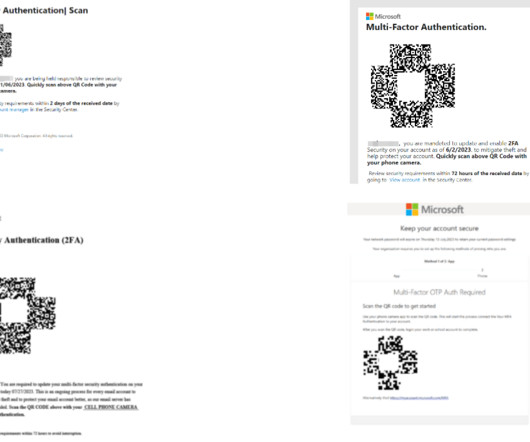
One may have assumed the first point of entry would be phishing gamers with fake logins and stealing their accounts. This is where additional security measures such as 2FA come in. A fake login site will ask for username and password, but then also ask the victim to enter their 2FA code on the phishing site.






















Let's personalize your content