Veeam Backup & Replication exploit reused in new Frag ransomware attack
Security Affairs
NOVEMBER 9, 2024
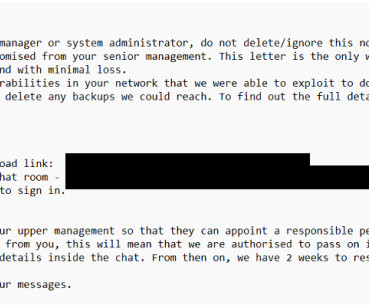
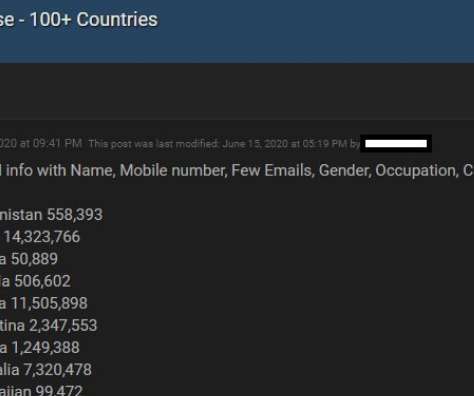
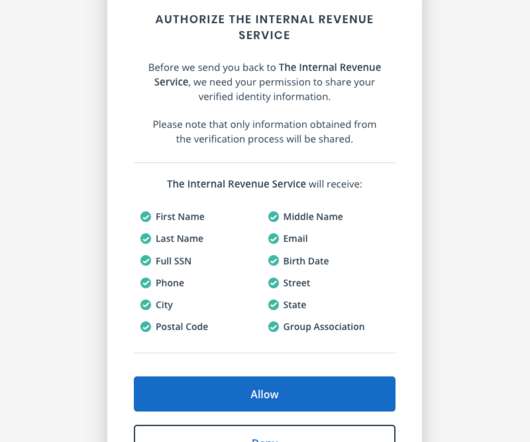
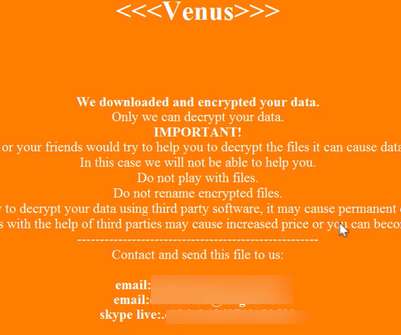
A critical flaw, tracked as CVE-2024-40711, in Veeam Backup & Replication (VBR) was also recently exploited to deploy Frag ransomware. In mid-October, Sophos researchers warned that ransomware operators are exploiting the critical vulnerability CVE-2024-40711 in Veeam Backup & Replication to create rogue accounts and deploy malware.











































Let's personalize your content