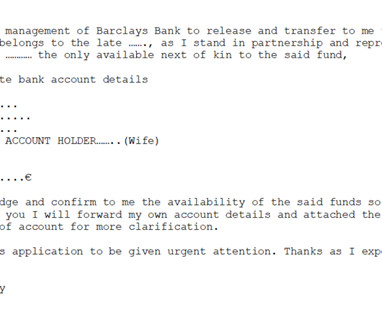
“Beyond the border scam”, pay attention to the instance of the new Nigerian fraud
Security Affairs
FEBRUARY 22, 2024
Following up on the electronic letter, the alleged widow begins a copious correspondence in which she says she was left completely alone after the death of her husband and children and without a home or money and hosted in a border refugee camp, where she feeds herself.





















Let's personalize your content