MY TAKE: A path for SMBs to achieve security maturity: start small controlling privileged accounts
The Last Watchdog
JUNE 23, 2021
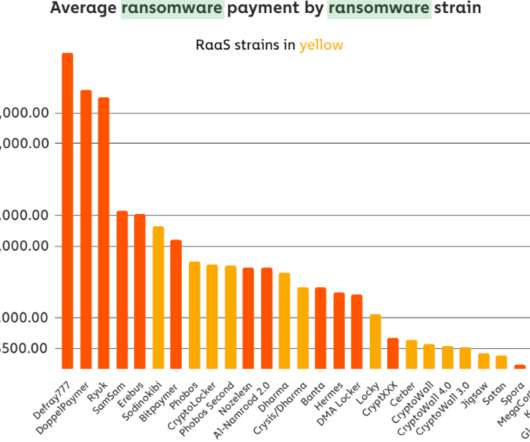
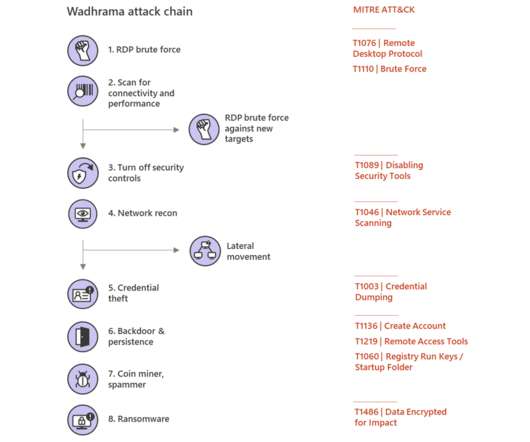
Here are the key takeaways: Lower-tier hacks. No organization wants to find itself having to recover from a devastating ransomware hack – or dealing with an unauthorized intruder who has usurped control of its operational systems. But that only served as a dinner bell to criminal hacking rings.



























Let's personalize your content