Account Hijacking Forum OGusers Hacked
Krebs on Security
MAY 18, 2019
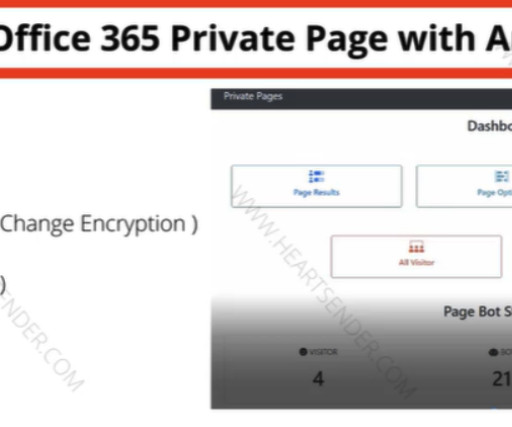
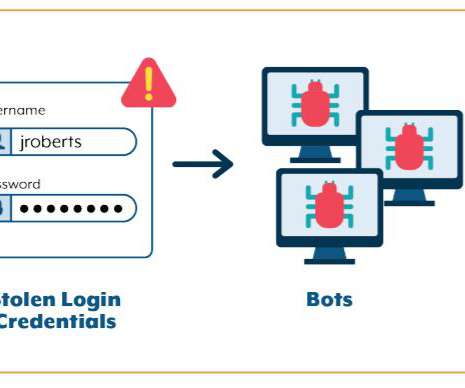
com — a forum popular among people involved in hijacking online accounts and conducting SIM swapping attacks to seize control over victims’ phone numbers — has itself been hacked, exposing the email addresses, hashed passwords, IP addresses and private messages for nearly 113,000 forum users.































Let's personalize your content