Deepfake and smishing. How hackers compromised the accounts of 27 Retool customers in the crypto industry
Security Affairs
SEPTEMBER 18, 2023
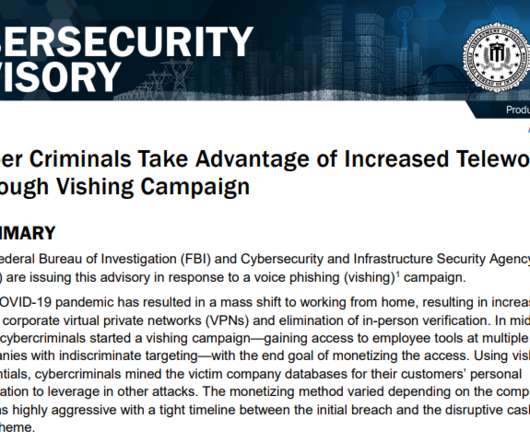
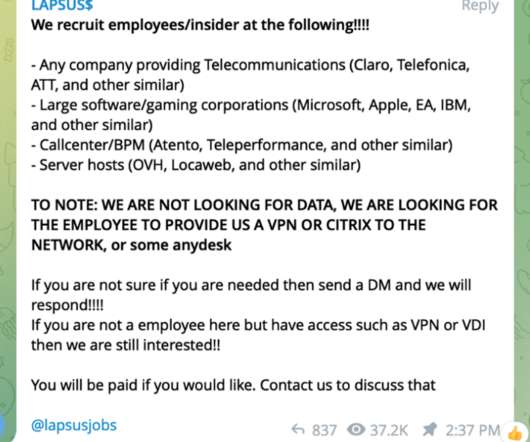
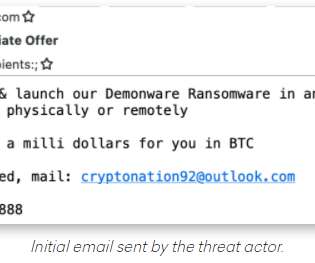
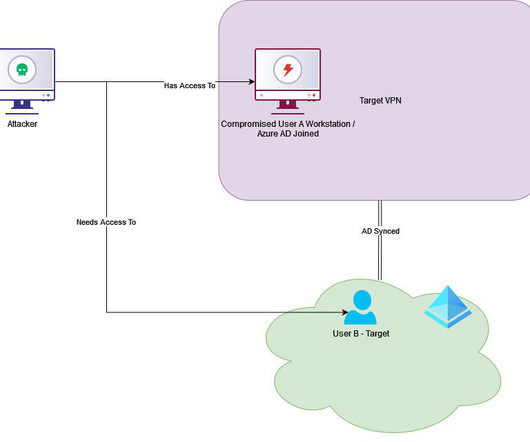
Software development company Retool was the victim of a smishing attack that resulted in the compromise of 27 accounts of its cloud customers. Software development company Retool revealed that 27 accounts of its cloud customers were compromised as a result of an SMS-based social engineering attack.






































Let's personalize your content