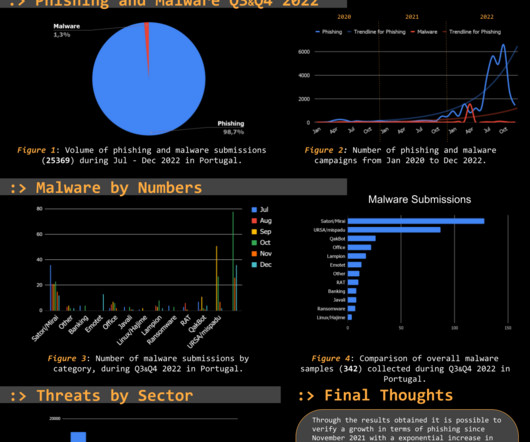
Threat Report Portugal: Q3 & Q4 2022
Security Affairs
APRIL 6, 2023
The Threat Report Portugal: H2 2022 compiles data collected on the malicious campaigns that occurred from July to December, H2, 2022. This makes it a reliable, trustworthy, continuously updated source, focused on the threats targeting Portuguese citizens. The submissions were classified as either phishing or malware.


















Let's personalize your content