macOS: Bashed Apples of Shlayer and Bundlore
Security Affairs
JULY 14, 2021
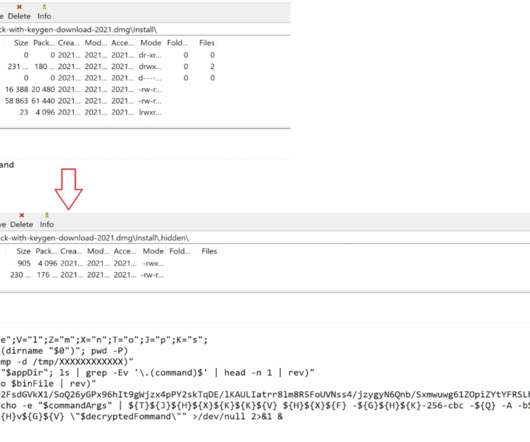
Though these scripts have slight variations, they mostly belong to a plague of adware strains— Shlayer and Bundlore. The malicious shell scripts used by Shlayer and Bundlore are usually malvertising-focused adware bundlers using shell scripts in the kill chain to download and install an adware payload.

























Let's personalize your content