Key Insights from the OpenText 2024 Threat Perspective
Webroot
MAY 6, 2024
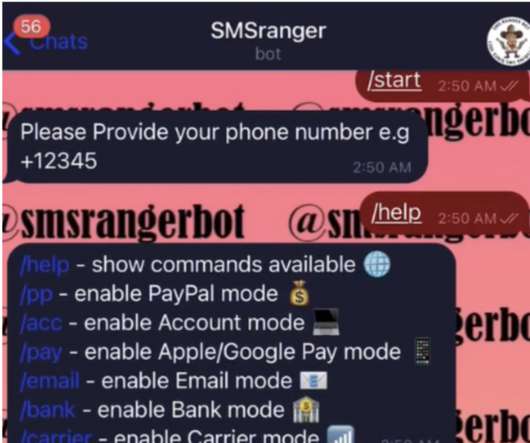
Keep all devices updated with the latest security patches, and use reputable antivirus solutions that can block suspicious downloads and identify malicious software. What was once a clear distinction between mass phishing emails and more targeted spear-phishing attempts is now blurring, making it harder to distinguish between the two.













































Let's personalize your content