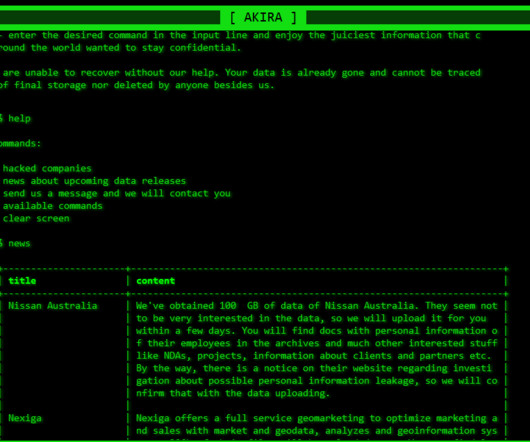
Akira ransomware received $42M in ransom payments from over 250 victims
Security Affairs
APRIL 21, 2024
The Akira ransomware operators implement a double extortion model by exfiltrating victims’ data before encrypting it. Earlier versions of the ransomware were written in C++ and the malware added the.akira extension to the encrypted files. “Akira threat actors utilize a sophisticated hybrid encryption scheme to lock data.














































Let's personalize your content