New Cactus ransomware encrypts itself to evade antivirus
Bleeping Computer
MAY 7, 2023
A new ransomware operation called Cactus has been exploiting vulnerabilities in VPN appliances for initial access to networks of "large commercial entities." [.]
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Bleeping Computer
MAY 7, 2023
A new ransomware operation called Cactus has been exploiting vulnerabilities in VPN appliances for initial access to networks of "large commercial entities." [.]

Tech Republic Security
JUNE 22, 2023
Protect your most sensitive data with this UltraVPN Secure USA VPN Proxy for 3 Years Subscription plus Free Antivirus for 30 Days while it’s available for just $30. The post Get three years of a powerful VPN plus 30 days of anti-virus protection for $30 appeared first on TechRepublic.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Quick Heal Antivirus
MARCH 18, 2021
VPN is a prominent tool for enhanced online life. VPN consists of a tunnel that your encrypted data. The post Data of 21 Million VPN users breached appeared first on Quick Heal Blog | Latest computer security news, tips, and advice.

eSecurity Planet
OCTOBER 27, 2021
What’s the best antivirus software? With the rise in malware and ransomware and a growing reliance on the internet, antivirus solutions are critical for protecting your data and applications. Top 4 antivirus software. Virtual private network ( VPN ). Encryption. Bitdefender. Other AV contenders.
Security Affairs
APRIL 7, 2021
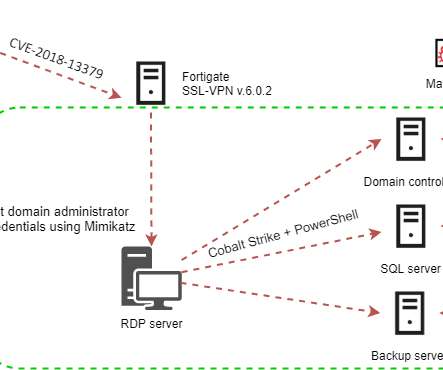
Attackers are actively exploiting the CVE-2018-13379 flaw in Fortinet VPN to deploy the Cring ransomware to organizations in the industrial sector. This ransomware encrypts data from victims with AES-256 + RSA-8192 and then demands a ~ 2 BTC ransom to get the files back. . SecurityAffairs – hacking, Fortinet VPN).
Security Affairs
APRIL 21, 2024
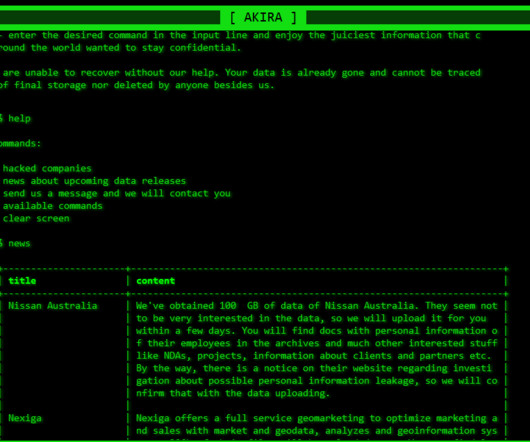
The Akira ransomware operators implement a double extortion model by exfiltrating victims’ data before encrypting it. Earlier versions of the ransomware were written in C++ and the malware added the.akira extension to the encrypted files. “Akira threat actors utilize a sophisticated hybrid encryption scheme to lock data.

eSecurity Planet
JANUARY 11, 2024
These devices exist outside of direct corporate management and provide a ransomware gang with unchecked platforms for encrypting data. How does remote encryption work? How Does Remote Encryption Work? Remote encryption performs ransomware encryption on a device beyond the security solutions monitoring for malicious activity.

The Last Watchdog
MARCH 6, 2021
Many people use a virtual private network (VPN) to bypass geographic restrictions on streaming sites or other location-specific content. Since a VPN tunnels traffic through a server in a location of your choosing. VPN’s can play another critical role, such as improving online privacy. Use antivirus software.
Security Affairs
MAY 9, 2023
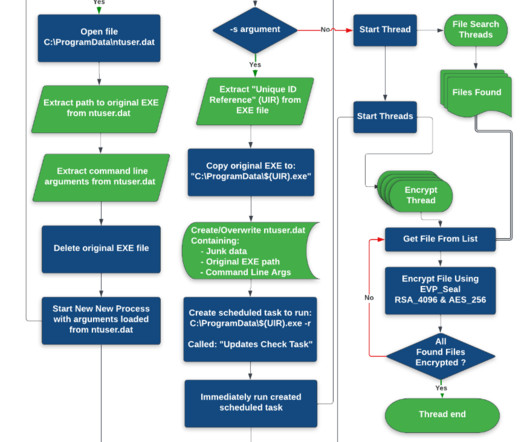
Researchers warn of a new ransomware family called CACTUS that exploits known vulnerabilities in VPN appliances to gain initial access to victims’ networks. The new ransomware strain outstands for the use of encryption to protect the ransomware binary. This technique allows the encryptor to avoid detection.

Identity IQ
MARCH 9, 2023
Use a VPN A VPN encrypts your traffic with military-grade encryption. A VPN also hides your IP address. Avoid Using File-Sharing Programs If you must use file-sharing programs, only do so over a VPN. If you must access sensitive information, be sure to use a VPN.

Identity IQ
MARCH 11, 2021
When inputting personal data, always make sure the URL is secure by making sure it starts with [link] The Hypertext Transfer Protocol Secure (HTTPS) designation indicates that the connection is encrypted and secure. Use a VPN . When using a VPN, your IP address is disguised and your connection is secure against external attacks.

CyberSecurity Insiders
FEBRUARY 9, 2021
You can achieve this by connecting to the internet through a VPN. This way, data is encrypted when passing through the internet, such that other people can’t read what is being sent. However, it is important to ensure that you are using a reliable VPN such as NordVPN. Use an antivirus. Be careful when sharing screens.
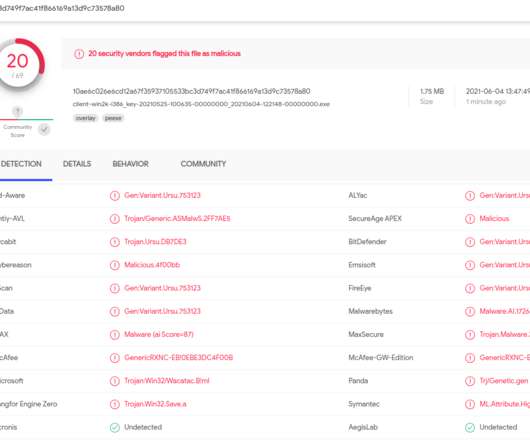
Security Boulevard
JUNE 7, 2021
In the process of doing so, I encountered a small snag: The FSB's website said in order to contact them securely, I needed to download and install an encryption and virtual private networking (VPN) appliance that is flagged by at least 20 antivirus products as malware.

Webroot
FEBRUARY 26, 2024
Safeguard your privacy with a trustworthy VPN In the digital-verse, protecting your online privacy is paramount, like guarding the secret recipe to your grandma’s famous carrot cake. That’s where a virtual private network (VPN) swoops in like a digital superhero to save the day. But fear not!

CyberSecurity Insiders
AUGUST 14, 2021
Use only encrypted networks. Most public networks are not encrypted, and it gives many chances to hackers for stealing any personal information. Most public networks are not encrypted, and it gives many chances to hackers for stealing any personal information. Use antivirus software to protect your computer.

CyberSecurity Insiders
JANUARY 11, 2022
Tools like a Virtual Private Network (VPN), two-factor authentication , and antivirus facilitate secure and smooth communication in an organization. Furthermore, a VPN application enables secure browsing and communication. Furthermore, a VPN application enables secure browsing and communication.

eSecurity Planet
MARCH 1, 2023
To prevent unwanted access and protect data in transit, wireless connections must be secured with strong authentication procedures, encryption protocols, access control rules, intrusion detection and prevention systems, and other security measures. As a result, wireless networks are prone to eavesdropping, illegal access and theft.

IT Security Guru
APRIL 26, 2021
Virtual Private Networks (VPN) are an ideal tool to mask sensitive information. They are commonly used to obscure one’s location, IP address, history, activity, and digital devices, making the VPN a very strong defence against identity theft threats. It is worth noting that antivirus software will only prevent against known threats.

SecureWorld News
JANUARY 21, 2024
Remember, sometimes a little common sense goes a lot further than the fanciest encryption out there. Ransomware is another significant threat, where attackers encrypt an organization's data and demand payment for its release. Nonprofits should also consider investing in a virtual private network, also known as a VPN.

Vipre
JANUARY 25, 2021
Thus, an antivirus is the most important security tool that everyone must have to protect themselves from viruses, malware, trojans, and similar cyber threats. Thus, an antivirus is the most important security tool that everyone must have to protect themselves from viruses, malware, trojans, and similar cyber threats.

The Last Watchdog
SEPTEMBER 6, 2023
Backups should be kept safely in several places, such as encrypted cloud storage or external hard drives. To avoid potential vulnerabilities, keep your operating system, antivirus software, and other security tools up to date. A virtual private network (VPN) can offer an additional layer of encryption and security.

Security Affairs
MARCH 19, 2022
The AvosLocker ransomware-as-a-service emerged in the threat landscape in September 2021, since January the group expanded its targets by implementing the support for encrypting Linux systems, specifically VMware ESXi servers. Install and regularly update antivirus software on all hosts, and enable real time detection.

CyberSecurity Insiders
JUNE 13, 2023
Learn about strong password creation, multi-factor authentica-tion, secure browsing habits, and data encryption. Avoid sharing sensitive information on public Wi-Fi networks and use a virtual private network (VPN) when connecting to public networks.

eSecurity Planet
DECEMBER 7, 2023
Encryption uses mathematical algorithms to transform and encode data so that only authorized parties can access it. What Encryption Is and How It Relates to Cryptology The science of cryptography studies codes, how to create them, and how to solve them. How Does Encryption Process Data? How Does Encryption Process Data?
Identity IQ
AUGUST 19, 2023
There are threats that can spread from one file to another, encrypt your files, or monitor what you do. When you update your antivirus software , you make sure it knows about the newest dangers, enabling it to protect your device. IdentityIQ offers antivirus with Bitdefender® Total Security. #2 First, check the website’s URL.

eSecurity Planet
AUGUST 22, 2023
Strong passwords, two-factor authentication, firewalls, encryption, and monitoring systems are just a few of the tools and procedures used to maintain security. Secure Communication Channels: When sending sensitive data outside of the company network, use encrypted communication tools (such as secure email and messaging applications).

CyberSecurity Insiders
APRIL 5, 2023
It’s more frequent within the older part of the population, who find even straightforward tasks, like running an antivirus scan, quite tedious. A VPN for PC could encrypt and reroute internet traffic but also block malicious websites. million is the cost of a data breach representing an increase of 2.6%

SecureWorld News
OCTOBER 22, 2023
Enforce enterprise-grade antivirus, firewalls, and internet security software across all connected devices. Utilize VPNs and encryption technologies Virtual Private Networks (VPNs) and encryption provide the core protections for remote employees to securely access internal systems and transmit sensitive data wherever they are working.

SecureWorld News
FEBRUARY 27, 2021
Invest in a strong VPN. A VPN can provide access to a remote company server, as well as other systems, tools, and software. But while VPNs can be extremely useful for businesses, they can also present issues if they are not managed effectively. Remote workers are more likely than ever to use a company virtual private network.
BH Consulting
FEBRUARY 23, 2023
Encrypt the data stored on your mobile phone. For Android, however, you may need to enable encryption manually. Remember to check that VPN is enabled and that MFA is also enabled for apps that support it. Change the default PIN code to connect to mobile phone Bluetooth. Re-install AV and set up cloud backups.

Webroot
OCTOBER 14, 2022
The year’s most successful ransomware group Introduced the triple extortion method – encryption + data leak + DDOS attack Accept payments in two untraceable cryptocurrencies Monero and Zcash as well as Bitcoin. Strategies for individuals.

Security Boulevard
JUNE 11, 2021
Start by installing antivirus software and use it to scan your system every week for malware and viruses. Always make it a point to update your antivirus software whenever a new version is available so you get the latest protection.

IT Security Guru
AUGUST 9, 2022
By acting as a “middleman” between your network and device – data transmitted through public Wi-Fi is rarely encrypted. Be cautious when you enter public wi-fi and use VPN to protect you from hacking techniques and phishing attacks. You can download a free antivirus program, though it is recommended that you buy one.

CyberSecurity Insiders
OCTOBER 29, 2021
The Dark Web Uses Encryption to Hide Locations. You can’t access the dark web through a typical search engine because dark websites use encryption to conceal their locations. Set up reliable antivirus programs and upgrade them as often as possible, especially if you work on a shared computer. Be Wary of Targeted Advertising.

eSecurity Planet
APRIL 19, 2023
For example, encryption keys, administrator passwords, and other critical information are stored in the Azure Key Vault in FIPS 140-2 Level 2-validated hardware security modules (HSMs).

Malwarebytes
APRIL 23, 2021
Pulse Secure VPN. According to its investigation, the threat actor connected to the entity’s network via a Pulse Secure Virtual Private Network (VPN) appliance. The cached credentials are normally protected by encryption unless they are marked as exportable. Maintain up-to-date antivirus signatures and engines.

Security Affairs
AUGUST 20, 2019
VPN or Virtual Private Network is the most secure way of connecting with the online world. VPN also provides an encrypted tunnel for all your online activities and closes all doors for spies and cybercriminals. VPN also provides an encrypted tunnel for all your online activities and closes all doors for spies and cybercriminals.
Identity IQ
DECEMBER 20, 2023
Hackers shifted their focus from encrypting files and demanding ransoms to simply stealing sensitive information and threatening to expose it, leaving victims with the crippling choice of financial ruin or possible public humiliation. But the numbers alone tell only part of the story.

Adam Levin
NOVEMBER 17, 2020
Leverage antivirus software. Protect yourself from malware by purchasing, updating, and upgrading antivirus software. VPNs encrypt data , making it much harder to intercept when transmitted through a shared or suspect internet connection. SSLs ensure all data is encrypted. Browse online using secure networks.

CyberSecurity Insiders
SEPTEMBER 14, 2021
Endpoint security – mobile device management (MDM) policies, antivirus (AV) solutions, URL filtering and blocking are all considered good cyber hygiene to block the most basic cyber threats. Use of a VPN – virtual private networks (VPN) create a secure connection to other networks over the internet.

Identity IQ
APRIL 12, 2023
Ransomware blocks an employer’s access to its data via encryption, and the employer will have to pay a ransom to access it. Connect to Secure Wi-Fi Employees should always connect to a secure Wi-Fi network that is encrypted and password protected. Malware and ransomware. Password theft.

Security Affairs
MAY 13, 2021
According to open-source reporting, since August 2020, DarkSide actors have been targeting multiple large, high-revenue organizations, resulting in the encryption and theft of sensitive data. Set antivirus/antimalware programs to conduct regular scans of IT network assets using up-to-date signatures.

eSecurity Planet
NOVEMBER 4, 2021
We use passwords to authenticate our users, run antivirus to keep malware off our endpoints , monitor our networks, and implement firewalls so we can have multiple defenses against attackers. In its default configurations, older versions of RDP do not use encryption to pass through credentials and session keys.

Security Affairs
NOVEMBER 19, 2019
To bypass antivirus systems, hackers send out malicious emails in non-working hours with delayed activation. Another technique used by cybercriminals to bypass antivirus systems is a targeted attack, in which malicious email are delivered outside regular working hours. More than 80% of all malicious files were disguised as .zip
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content