ClamAV Issues Urgent Patch for High-Risk DoS Vulnerability CVE-2024-20380
Penetration Testing
APRIL 18, 2024
The ClamAV development team has released urgent security patches for its popular open-source antivirus software.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Penetration Testing
APRIL 18, 2024
The ClamAV development team has released urgent security patches for its popular open-source antivirus software.

The Last Watchdog
JULY 11, 2023
Conduct regular penetration testing. Regular and thorough penetration testing is crucial for identifying vulnerabilities within trading systems. Employ real-time antivirus scanning. Encryption renders data unreadable to unauthorized individuals, significantly reducing the risk of data breaches.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

eSecurity Planet
FEBRUARY 23, 2022
These are not uncommon risks. The devices themselves can’t be secured, but that doesn’t mean we can’t use basic IT techniques to reduce our security risks. A report from this year estimates that 53% of connected medical devices have an identified critical risk. This includes 73% of IV pumps and most laboratory devices.

eSecurity Planet
APRIL 18, 2022
During such reconnaissance operations, attackers collect relevant data about their victims, but it’s not without risks for them. Also read: Best Penetration Testing Tools. Top Open Source Penetration Testing Tools. What Data Do Hackers Collect? Domain names, subdomains, CDN, mail servers, and other hosts.

SecureWorld News
OCTOBER 22, 2023
Going global or even expanding your operations further afield in your geography introduces a host of new digital risks. These risks require proactive and methodical strategizing to overcome if you are to protect your assets, data, and reputation. Categorize data sensitivity levels and legal or regulatory compliance requirements.

Cytelligence
NOVEMBER 16, 2023
In today’s digital landscape, cyber threats pose a significant risk to organizations of all sizes. It provides a structured approach to assess and manage cybersecurity risks, allowing organizations to align their security efforts with business objectives.

Zigrin Security
OCTOBER 11, 2023
By understanding their motivations, we can better comprehend the risks and develop effective strategies to protect ourselves. Implement Firewalls and Antivirus Software Firewalls act as a barrier between your internal network and the external internet, monitoring and blocking unauthorized access.
Spinone
NOVEMBER 19, 2020
Examples: Software without compliance certification ; Applications that aren’t updated on a regular basis; Lack of antivirus software. Conduct penetration testing once in a while. Install antivirus software and tools that detect shadow IT. Human error vulnerabilities Human errors are inevitable.

NopSec
AUGUST 23, 2022
What a cybersecurity team is striving for is understanding and managing the risks their organization faces. If you pick it apart, you can see that risk is the result of vulnerabilities and threats. That’s how risk is assessed. But risk is not classified into a simple yes or no answer.

eSecurity Planet
FEBRUARY 2, 2024
And IoT devices often don’t have the firmware to install antivirus software or other protective tools. Physical Access Systems Cybersecurity risk management vendor OTORIO presented research on physical access systems — like keycard readers — at the 2023 Black Hat Europe conference in December.

SecureWorld News
FEBRUARY 27, 2022
It was once the case that the majority of businesses could rely on a good firewall and antivirus solution. Indeed, while antivirus and firewall software do still play an important role in cybersecurity, they are not enough on their own. Using penetration testing as well as other forms of ethical hacking is a great way to do this.

eSecurity Planet
APRIL 30, 2024
Prepare for Installation The first stage in setting up a firewall is to prepare for installation after evaluating the type of firewall you need via the risk assessment listed above. Configure Logging & Alerts Recording and monitoring firewall activity makes sure that security risks or operational concerns are detected in a timely manner.

Malwarebytes
MAY 19, 2022
Default configurations are now running the risk of bans and fines. RDP, NetBios, and Telnet are all potentially high-risk for an insecure network. Use antivirus solutions : Workstations require security solutions capable of dealing with exploits that require no user interaction and attacks reliant on social engineering.

Centraleyes
JANUARY 7, 2024
There’s no avoiding digital risk. However, that doesn’t mean there aren’t plenty of ways to minimize these risks. It’s important your cybersecurity teams have a cyber risk management program in place for this purpose. Efficient risk and vulnerability assessment is another area where automation shines.

eSecurity Planet
AUGUST 22, 2023
Regular Security Audits: Security audits using vulnerability scans or penetration tests should be conducted regularly to detect vulnerabilities and verify that security rules are properly implemented and followed. Secure File Sharing and Collaboration Tools: Secure file-sharing platforms are necessary for collaborative work.

SecureList
DECEMBER 14, 2020
They provide reliable protection against malware and, when combined with relevant policies, regular updates, and employee cyberhygiene, they can shield a business from a majority of cyber-risks. Legitimate software can hide risks. For some, it may seem like you do not need more security than this… But is that really the case?

eSecurity Planet
MARCH 17, 2023
From there, these tools send alerts to security teams if and when risks are identified. Vulnerability management is handled not only by cybersecurity and IT teams but by cross-functional teams that understand how assets are used across the organization.

eSecurity Planet
AUGUST 22, 2023
Even the largest organizations with the most robust internal security teams will engage with MSSPs for specialty projects, penetration tests, and other specific needs. Managed endpoint security installs, configures, and maintains endpoint protection tools ( antivirus , endpoint detection and response (EDR), etc.)

Security Boulevard
MARCH 31, 2021
conduct employee phishing tests. conduct penetration testing. The Microsoft Exchange hack: Microsoft Probes Whether Leak Played Role in Suspected Chinese Hack - The risks and rewards of sharing bug intel. Microsoft Antivirus Now Automatically Mitigates Exchange Server Vulnerability.

SiteLock
OCTOBER 12, 2021
Providers stick to uniform risk mitigations and abide by most security rules. David Balaban is a computer security researcher with over 17 years of experience in malware analysis and antivirus software evaluation. Looking Into The Future. It is a good decision to let a provider manage your data and computation power.
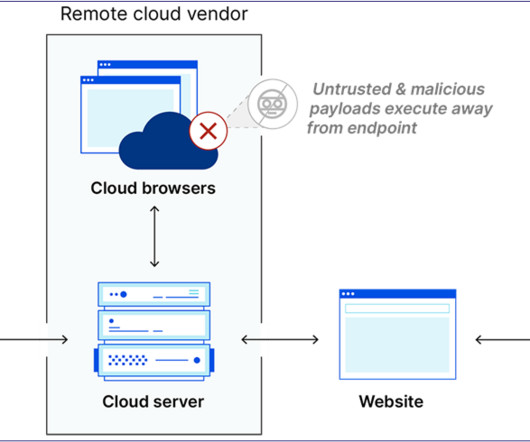
Security Boulevard
JANUARY 17, 2024
Browser isolation is a security concept in which a user’s web traffic is isolated in a virtual machine, hosted web browser, or some other manner to prevent malicious activities from reaching the end user; thereby lowering the general risk of web browsing. Antivirus Inspection Not all RBI products will prioritize this time factor.

ForAllSecure
APRIL 26, 2023
How to Protect Against Social Engineering Attacks Organizations can protect themselves against social engineering attacks by educating employees about the risks, enabling multi-factor authentication, and implementing security policies that require verification of any requests for sensitive information or actions.

SiteLock
OCTOBER 21, 2021
The most significant types of attacks are described in the OWASP Top Ten Web Application Security Risks (for web applications) and OWASP API Security Top Ten (for API services). David Balaban is a computer security researcher with over 17 years of experience in malware analysis and antivirus software evaluation.

eSecurity Planet
MARCH 14, 2023
Often auditing will be performed through the review of networking logs, but penetration testing and vulnerability scanning can also be used to check for proper implementation and configuration. Endpoint security : protects endpoints with antivirus, endpoint detection and response (EDR) tools, etc. for unauthorized access.

eSecurity Planet
DECEMBER 18, 2023
Access restrictions, network settings, and security group rules are all at risk of misconfiguration. Regular security audits, adherence to best practices, and extensive user training are critical methods for identifying and correcting misconfigurations and limiting related risks. This reduces the chance of successful assaults.

eSecurity Planet
APRIL 26, 2024
Cloud infrastructure entitlement management (CIEM): Manages compliance, risk, and security with controlled user, system, and app cloud resource access. The security controls include: Antivirus (AV): Scans for malware based on a database of known-malicious file signatures to provide basic defense against common attacks.

eSecurity Planet
DECEMBER 3, 2021
Russian software engineer Eugene Kaspersky’s frustration with the malware of the 80s and 90s led to the founding of antivirus and cybersecurity vendor Kaspersky Lab. Graham Cluley started as a videogame developer and antivirus programmer three decades ago before serving in senior roles at Sophos and McAfee. Street @jaysonstreet.

NetSpi Executives
APRIL 27, 2024
Do antivirus and endpoint detection and response (EDR) tools stop ransomware? Only about 20% of the ransomware tactics, techniques, and procedures (TTP) used by ransomware attackers are identified out-of-the-box by antivirus (AV), endpoint detection and response (EDR), and security information and event management (SIEM) tools.

SecureList
DECEMBER 11, 2023
In Europe, efforts are underway to craft the EU AI Act , which introduces a risk-based approach for classification of AI systems. Cybersecurity risks and vulnerabilities As any other technological advancement, along with exciting opportunities, generative AI brings new risks into the equation.

eSecurity Planet
MARCH 22, 2023
Penetration testing and vulnerability scanning should be used to test proper implementation and configuration. Better network security access controls can improve security and decrease cost and risk. In the event of device failure, backups can reduce the risk of business disruption by accelerating recovery.

IT Security Guru
JULY 19, 2021
This also results in a higher level of risk to organisations with most home networks undeniably easier to hack into than office networks. Ensure you have antivirus and firewalls deployed and enabled on all endpoints, especially if using your own personal devices. That list is continually expanding as more vulnerabilities are found.

eSecurity Planet
AUGUST 9, 2023
For example, the credit card industry’s PCI DSS requirements force organizations to use vendors unaffiliated with implementing IT infrastructure to conduct penetration testing. Where required, the MSP will also install software related to the service to be performed (antivirus, network monitoring software, etc.).

eSecurity Planet
AUGUST 9, 2023
For example, the credit card industry’s PCI DSS requirements force organizations to use vendors unaffiliated with implementing IT infrastructure to conduct penetration testing. Where required, the MSP will also install software related to the service to be performed (antivirus, network monitoring software, etc.).

eSecurity Planet
MAY 20, 2022
All it takes is one individual to not be careful with their cybersecurity to put the others at risk. See our picks for the the Best Antivirus Software. Also read: Cybersecurity Risks of 5G – And How to Control Them. 18 Top Wi-Fi Testing Tools – Free and Paid. Such challenges exist in the office, too.

SecureWorld News
SEPTEMBER 30, 2020
CISOs worry about the latest incident, end of life technology in their environment, breaches in the news, insecure users and vendors, penetration testing results, budget and resources, and the latest vulnerability report (to name a few). For example, would you use antivirus alone as an endpoint security solution?

Cytelligence
FEBRUARY 25, 2023
As the number of IoT devices increases, so does the risk of cyber-attacks. Ensure that your antivirus and anti-malware software is up to date and regularly run scans to detect any potential threats.

eSecurity Planet
DECEMBER 8, 2023
Organizations that manage their own servers will need to isolate, harden, maintain, and audit DNS servers the same as they would any other high-risk server managing sensitive information. Attackers regularly target DNS servers and services which categorizes DNS servers as high risk, high value, and high likelihood for attack.

eSecurity Planet
MAY 2, 2024
Risk-based analytics: Considers the level of risk as the context for the level of permission needed to access systems, applications, and data. Endpoint protection platform (EPP) and Endpoint detection and response (EDR) : Add features to antivirus to detect malicious behavior and proactively block attacks.

ForAllSecure
FEBRUARY 8, 2023
So basically, we deliver custom penetration tests. For example, some of our tools are actually recognized by various antivirus services, not because they contain a virus, but because it's considered to be a hacking tool, which we definitely use for our pandas. Being on the good side and also on the bad side. And secure Academy.

eSecurity Planet
JANUARY 11, 2022
Boasting itself as the world’s first Code Risk Platform, Apiiro Security offers risk visibility across design, code, and cloud segments. Apiiro can connect across hybrid infrastructure through a read-only API and promises real-time inventory and actionable remediation for risks in addressing DevSecOps. Apiiro Security.
Krebs on Security
MARCH 4, 2022
The leaked chats show that the Conti group — which fluctuated in size from 65 to more than 100 employees — budgeted several thousand dollars each month to pay for a slew of security and antivirus tools. “They are insured for cyber risks, so what are we waiting for?”

eSecurity Planet
APRIL 26, 2022
Company Sector Year Status Vicarius Vulnerability management 2022 Private Dragos ICS and OT security 2021 Private Safeguard Cyber Risk management 2021 Private CyberGRX Risk management 2019 Private Signifyd Fraud protection 2018 Private RedOwl Security analytics 2015 Acquired: Forcepoint. AllegisCyber Investments. BVP Investments.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content