Legacy Authentication Protocols: Why RADIUS Is (Still) Important
Duo's Security Blog
MAY 23, 2024
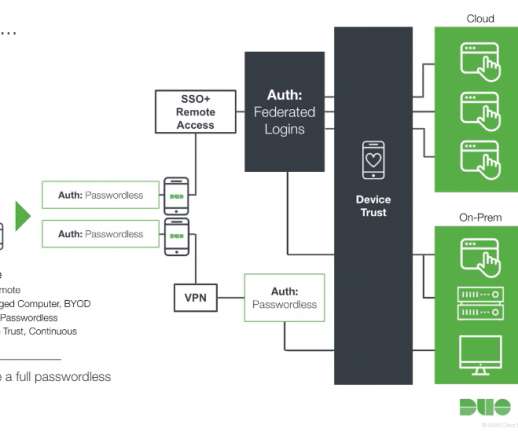
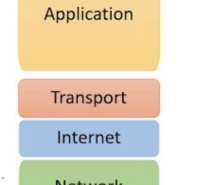
When reading the title of this blog, you might be wondering to yourself why RADIUS is being highlighted as a subject — especially amidst all of the advancements of modern authentication we see taking place recently. Instead, it supports a variety of authentication protocols , including EAP, PAP, CHAP, and others. What is RADIUS?









































Let's personalize your content