Cybersecurity Research Topics for Beginners: Exploring the Fundamentals
CyberSecurity Insiders
MAY 28, 2023
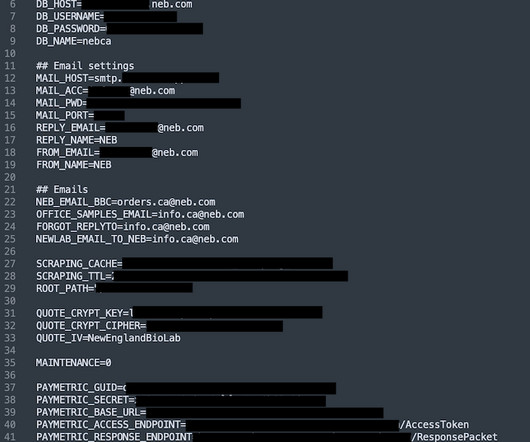
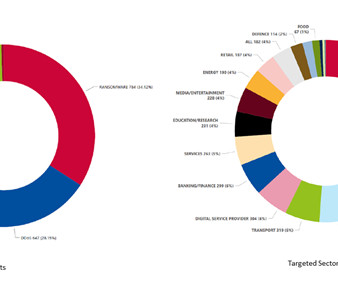
Network Security: Study network protocols, such as TCP/IP, and analyze common network attacks like DDoS, phishing, and man-in-the-middle attacks. Cryptography: Dive into the world of cryptography, studying symmetric and asymmetric encryption, digital signatures, and cryptographic algorithms.




















Let's personalize your content