Cuttlefish malware targets enterprise-grade SOHO routers
Security Affairs
MAY 1, 2024
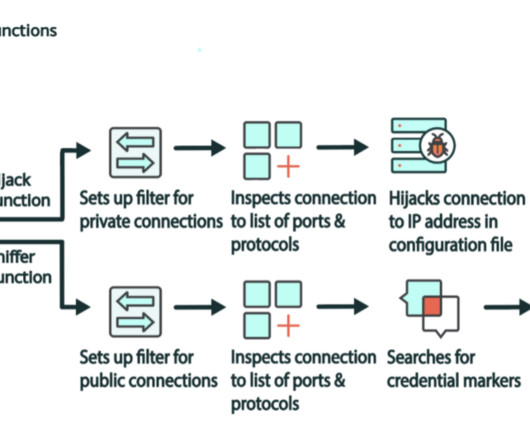
The malicious code can also perform DNS and HTTP hijacking within private IP spaces. “What makes this malware family so insidious is the ability to perform HTTP and DNS hijacking for connections to private IP addresses. The binary analyzed by the researchers is compiled for all major architectures used by SOHO operating systems.





















Let's personalize your content