CISO workshop slides
Notice Bored
AUGUST 5, 2022
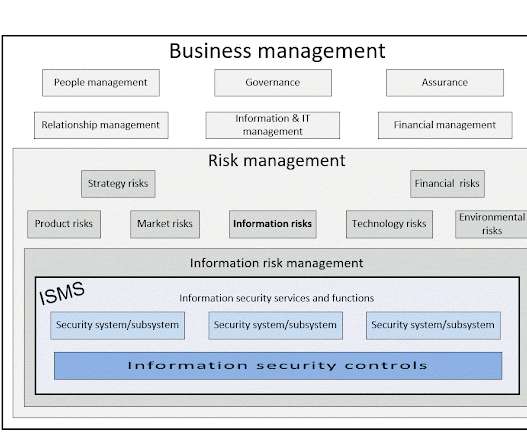
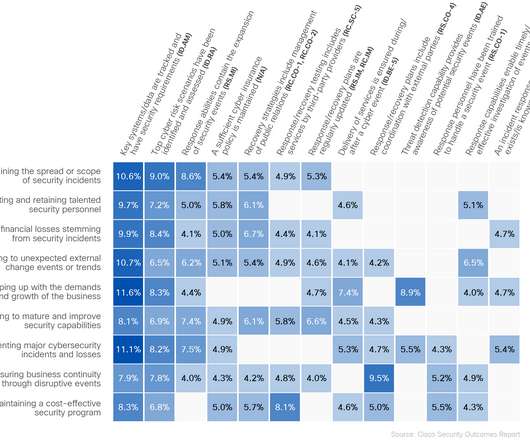
Generally, though, the risk management and security arrangements quietly support and enable the business from the inside, as it were, rather than being exposed externally - unless they fail anyway! including security-relevant aspects ( e.g. being a trusted partner). Security Response : the example metrics suggest the classical (outdated!)




















Let's personalize your content