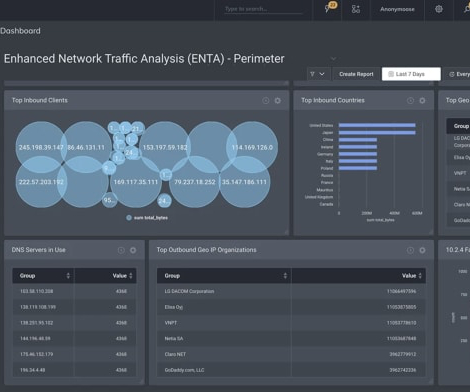
Zero Trust Architecture: Enhancing Network Security
SecureBlitz
AUGUST 3, 2023
Here, I will talk about how Zero Trust Architecture enhances network security. In today's digital landscape, where cyber threats are becoming increasingly sophisticated, traditional security measures are no longer sufficient to safeguard sensitive information.













































Let's personalize your content