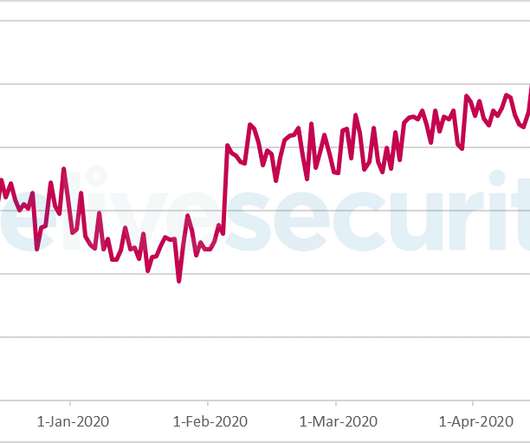
Hackers take over 1.1 million accounts by trying reused passwords
Malwarebytes
JANUARY 6, 2022
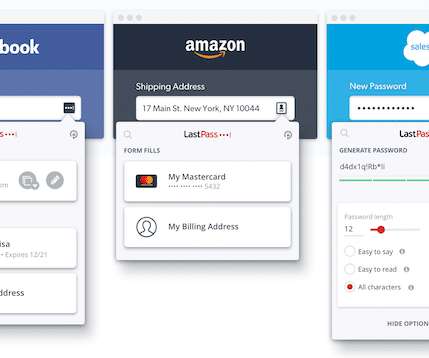
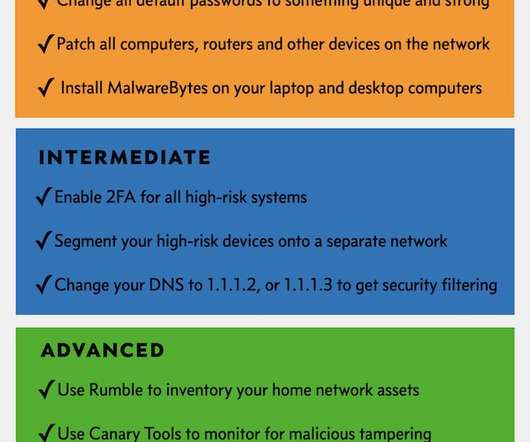
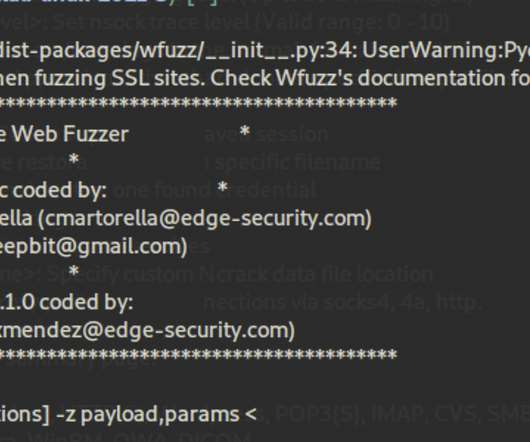
Credential stuffing is the automated injection of stolen username and password pairs in to website login forms, in order to fraudulently gain access to user accounts. Besides listening to us telling you that you should not reuse passwords across multiple platforms, there are some other thing you can do. Start using a password manager.










































Let's personalize your content