MY TAKE: Why monetizing data lakes will require applying ‘attribute-based’ access rules to encryption
The Last Watchdog
JUNE 2, 2021
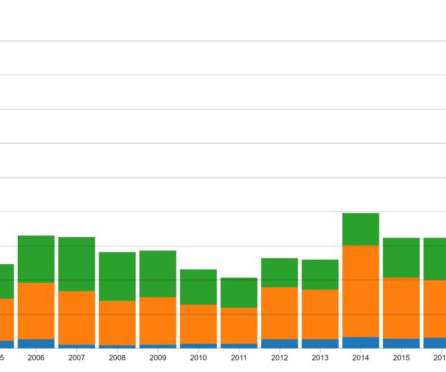
The amount of data in the world topped an astounding 59 zetabytes in 2020, much of it pooling in data lakes. We’ve barely scratched the surface of applying artificial intelligence and advanced data analytics to the raw data collecting in these gargantuan cloud-storage structures erected by Amazon, Microsoft and Google.











Let's personalize your content