Citrix Bleed widely exploitated, warn government agencies
Malwarebytes
NOVEMBER 24, 2023
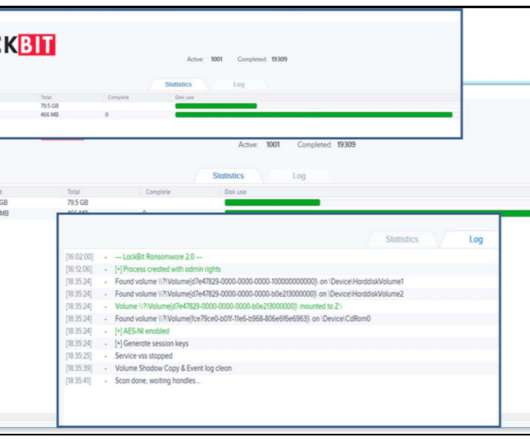
The vulnerability provides attackers with the capability to bypass multi-factor authentication (MFA) and hijack legitimate user sessions, and is said to be very easy to exploit. Customers using Citrix-managed cloud services or Citrix-managed Adaptive Authentication products are not impacted. Stop malicious encryption.















































Let's personalize your content