U.S. CISA adds Veeam Backup and Replication flaw to its Known Exploited Vulnerabilities catalog
Security Affairs
OCTOBER 19, 2024
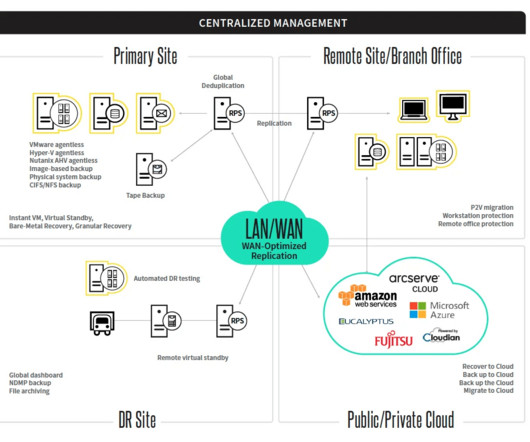
Cybersecurity and Infrastructure Security Agency (CISA) adds Veeam Backup and Replication vulnerability to its Known Exploited Vulnerabilities catalog. Cybersecurity and Infrastructure Security Agency (CISA) added the Veeam Backup and Replication flaw CVE-2024-40711 (CVSS score of 9.8) impacting Veeam Backup & Replication (VBR).












































Let's personalize your content