SHARING INTEL: Here’s why it has become so vital to prioritize the security-proofing of APIs
The Last Watchdog
NOVEMBER 30, 2021
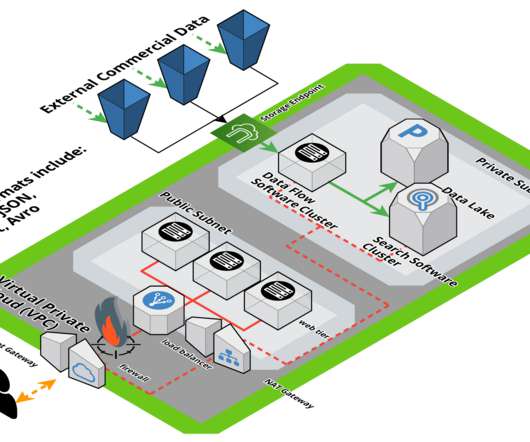
Cyber assaults – from data theft to credential stuffing to account take over — today often start with legitimately accessing a client-facing application and then manipulating an API to extract valuable data, launch a DoS attack, or perform an account takeover. A startling 95% of API attacks happen on authenticated endpoints.



















Let's personalize your content