Critical Success Factors to Widespread Deployment of IoT
Thales Cloud Protection & Licensing
FEBRUARY 16, 2021
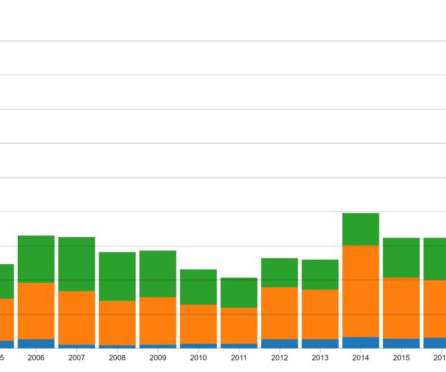
Critical Success Factors to Widespread Deployment of IoT. Digital technology and connected IoT devices have proliferated across industries and into our daily lives. Finally, IoT devices are being used extensively in smart vehicles and home appliances to provide enhanced user experiences. Threat vectors on IoT.





























Let's personalize your content