How to defend your organization against social engineering attacks
Tech Republic Security
NOVEMBER 5, 2020
A security awareness program backed by multi-factor authentication can help protect your critical assets, says NordVPN Teams.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Tech Republic Security
NOVEMBER 5, 2020
A security awareness program backed by multi-factor authentication can help protect your critical assets, says NordVPN Teams.

SC Magazine
MAY 4, 2021
Infosec’s Choose Your Own Adventure training game “Deep Space Danger” tests employees on their knowledge of social engineering. The employees at your organization are badly in need of security awareness training. Two of them are fraudsters trying to socially engineer their way onto the station.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Spinone
NOVEMBER 12, 2020
What is social engineering? Social engineering is a manipulative technique used by criminals to elicit specific actions in their victims. Social engineering is seldom a stand-alone operation. money from a bank account) or use it for other social engineering types.

Thales Cloud Protection & Licensing
OCTOBER 24, 2022
Cyber Security Awareness Month: Time to Act and Protect Trust. We’re approaching the end of Cyber Security Awareness Month , an annual event dedicated to increasing awareness of cybersecurity topics globally. Cybercriminals increasingly employ social engineering tactics because they are effective.

SecureWorld News
MARCH 21, 2024
March Madness is a prime opportunity for cybercriminals to deploy phishing lures, malicious apps, and social engineering tactics," warns Krishna Vishnubhotla, VP of Product Strategy at mobile security firm Zimperium.

Approachable Cyber Threats
SEPTEMBER 24, 2022
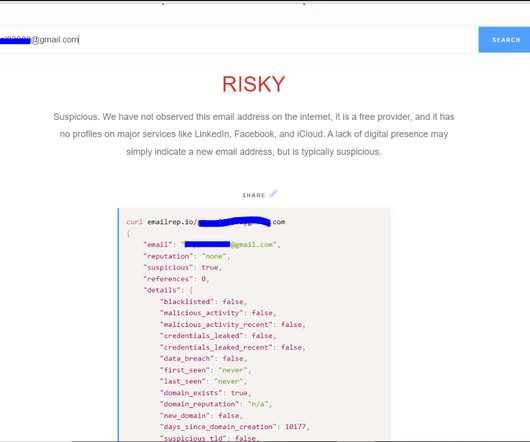
Category News, Social Engineering. All of the attacks were carried out with relatively simple phishing and social engineering techniques. After getting an Uber employee’s login credentials, likely purchased from the dark web, the hacker then used social engineering to get around Uber’s multi-factor authentication.
SecureWorld News
JUNE 6, 2023
These attacks can come from malicious instructions, social engineering, or authentication attacks, as well as heavy network traffic. Defending against phishing The general defense methods for protecting oneself against an attack can be thought of as the pillars that support your overall security online.

Security Through Education
MARCH 4, 2024
In prepping for my speech, I realized that the techniques I daily use as a certified social engineer equipped me more than I realized. Influence Techniques At Social-Engineer, you may often hear or read about us referring to “Influence Techniques.” However, speaking to an audience is a whole different beast.
Security Boulevard
APRIL 16, 2024
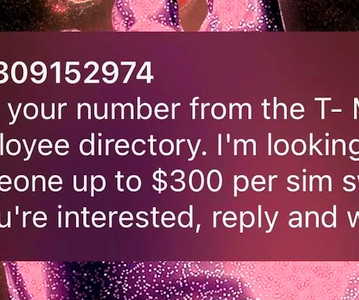
Not OK: SMS 2FA — Widespread spam targets carrier employees, as scrotes try harder to evade two-factor authentication. The post SIM Swappers Try Bribing T-Mobile and Verizon Staff $300 appeared first on Security Boulevard.

Krebs on Security
AUGUST 19, 2020
Allen said a typical voice phishing or “vishing” attack by this group involves at least two perpetrators: One who is social engineering the target over the phone, and another co-conspirator who takes any credentials entered at the phishing page and quickly uses them to log in to the target company’s VPN platform in real-time.

CyberSecurity Insiders
MARCH 23, 2021
Lack of awareness, budget issues and other factors are paving way to more cyber attacks on Maritime industry say experts as malware and phishing continue to rule the chart- both launched through social engineering attacks.

SecureWorld News
NOVEMBER 8, 2023
Social engineering attacks have long been a threat to businesses worldwide, statistically comprising roughly 98% of cyberattacks worldwide. Given the much more psychologically focused and methodical ways that social engineering attacks can be conducted, it makes spotting them hard to do.

SecureWorld News
AUGUST 5, 2023
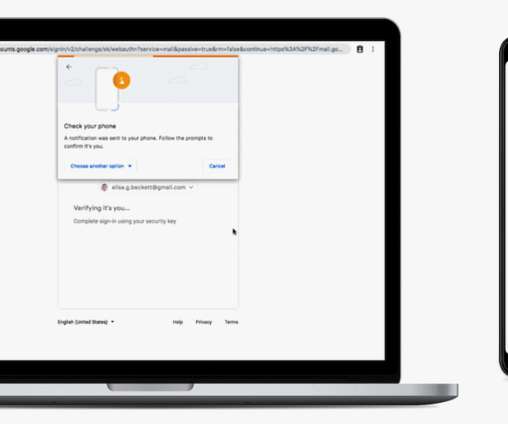
Multi-factor authentication (MFA) is a fundamental component of best practices for account security. Traditionally, this approach to authentication delivers a unique code to a user's email or phone, which is then inputted following the account password. SMS-based MFA MFA via SMS (i.e.,

BH Consulting
AUGUST 16, 2023
This could include malware that antivirus and security solutions can’t detect; a secure internet connection to prevent tracing; initial access to victim companies’ networks or mailboxes (which is also key to many ransomware infections); effective social engineering content; fraudulent content hosting, and more.

eSecurity Planet
AUGUST 23, 2023
This method involves using emails, social media, instant messaging, and other platforms to manipulate users into revealing personal information or performing actions that can lead to network compromise, data loss, or financial harm. The likelihood that the target will respond to a message is increased by this personalization.

CyberSecurity Insiders
APRIL 16, 2021
The emails pose as company updates and are often socially engineered to look like they have been personally tailored to the recipient. The kind that could throw off even your most security-aware employees. Carefully crafted emails like these containing a malicious link can fool even the most security-aware of employees.

CyberSecurity Insiders
APRIL 10, 2023
Why is identity management and security important in 2023? “In In the current digital landscape, identity security has gained paramount importance due to the growing cyber risks posed by phishing and social engineering attacks utilizing AI. Security awareness programs for all employees.

Security Boulevard
APRIL 25, 2023
Google Authenticator app now syncs your secrets: No stress if you break your phone. Google Makes 2FA App Useable — BUT There’s a Catch appeared first on Security Boulevard. 2FA OTP ASAP? The post FINALLY!
Pen Test Partners
FEBRUARY 14, 2024
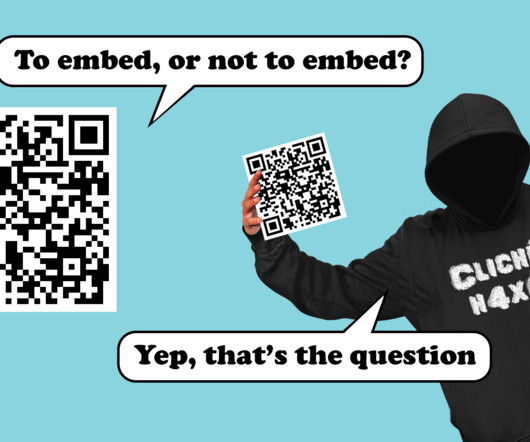
October 2023’s Cyber Security Awareness Month led to a flurry of blog posts about a new attack called Quishing (QR Code phishing) and how new AI powered email gateways can potentially block these attacks. Currently, most initial access attempts are carried out with social engineering, commonly phishing. Why is that?

SecureWorld News
JUNE 16, 2021
If someone is in your organization's Slack channel, then they are authenticated and the environment is secure. The group was able to steal the source code for FIFA 21 and the source code for the Frostbite engine that powers other popular games, such as Battlefield. You want to believe it is true.

SecureWorld News
JULY 31, 2020
Since the attack occurred in early July, speculation about how hackers compromised Twitter's security have run rampant, especially on.Twitter. Even the title of SecureWorld's first story about the incident had questions: "Famous Twitter Accounts Hacked: Insider Threat or Social Engineering Attack?". How was Twitter hacked?

SecureWorld News
JUNE 16, 2021
If someone is in your organization's Slack channel, then they are authenticated and the environment is secure. The group was able to steal the source code for FIFA 21 and the source code for the Frostbite engine that powers other popular games, such as Battlefield. You want to believe it is true.

The Last Watchdog
FEBRUARY 3, 2021
We may think we know how to recognize a social engineering attack or phishing email, but with the amount of information available to attackers through open platforms and stolen information, they may know far more about us than we realize. I always recommend, if there’s an option with multi factor authentication, to NOT go by SMS.

SC Magazine
JUNE 24, 2021
A new blog post report has shone a light on the malicious practice known as voice phishing or vishing – a social engineering tactic that some cyber experts say has only grown in prominence since COVID-19 forced employees to work from home. (Ser Amantio di Nicolao, CC BY-SA 3.0 , via Wikimedia Commons).
Hacker's King
JUNE 27, 2023
You may also like: Top Methods Used By Hackers To Bypass 2F-Authentication What is OSINT? It involves gathering and analyzing data from publicly accessible sources such as websites, social media platforms, news articles, and public records. . Let’s explore how OSINT works and its practical applications.

SecureWorld News
MAY 22, 2023
It was an old-school use of mirrored websites and social engineering to get USPS employees to enter their information into a fraudulent website. Randy Watkins, CTO at Critical Start, said: "This attack is an unfortunate example of exploitation of lacking foundational security controls.

Security Boulevard
MAY 20, 2021
That “Microsoft Authenticator” extension you installed is actually malware, designed to phish for your passwords. The post Fake Chrome Extensions: Google Asleep at the Switch appeared first on Security Boulevard.
Security Boulevard
FEBRUARY 10, 2022
Google started auto-enrolling users in two-factor authentication (2FA) nine months ago. appeared first on Security Boulevard. And now it’s releasing the results: Account breaches halved. The post Google Lauds 2FA Results—So Why do People HATE It?

SC Magazine
FEBRUARY 4, 2021
You really want to try to limit the level of information you share because everything you put in that out-of-office reply can be used to provide context or make a social engineering attack even more convincing, said Tim Sadler, co-founder and CEO at Tessian. At the end of the day, promoting security awareness is paramount.

SecureList
MAY 6, 2024
The attackers employed social engineering techniques to trick victims into sharing their financial data or making a payment on a fake page. Fake Louis Vuitton store on Instagram As new and more secure, authentication technologies appear, scammers find ways to evade these, too.

The Last Watchdog
APRIL 10, 2019
Organizations like OneSpan now analyze bank fraud through the mobile app landscape through areas like social engineering attacks, screen captures, or changing SIM cards, LaSala told me. A solution will recognize that the user is always using the same device and allows for a more seamless authentication path.

Security Boulevard
SEPTEMBER 19, 2022
A spate of thefts from gym lockers is reminding us that SMS based two-factor authentication (2FA) is utter, UTTER garbage. The post Victims of Gym Phone Theft Lose $10,000 Each (Because SMS 2FA) appeared first on Security Boulevard.

SC Magazine
JUNE 21, 2021
From direct assaults on passwords via brute force attacks and password spraying to email phishing, ransomware and social engineering campaigns that act as precursors to credential stuffing attacks, adversaries are well aware that the path of least resistance almost always involves the compromising of a password.

Malwarebytes
MAY 23, 2023
Threat actors often gain initial access to a network through exposed and poorly secured remote services , and later traverse the network using the native Windows RDP client. Implement phishing-resistant multi-factor authentication (MFA) for all services, particularly for email, VPNs, and accounts that access critical systems.

Security Boulevard
JUNE 1, 2022
Other components of a good cybersecurity posture include two-factor authentication and continuous cybersecurity monitoring. Collecting security events from across your IT infrastructure, network, and applications, and reporting threats on a constant basis, are integral to enterprise network safety. Fiction: Strong passwords are enough.

SC Magazine
JULY 9, 2021
The abundance of personal information available online — including audio and video samples of business leaders — has already made it easier for threat actors to carry out social engineering attacks. However, by combining this data with deepfakes, cybercriminals can theoretically create almost undetectable phishing attacks.

eSecurity Planet
DECEMBER 7, 2022
He has over 20 years experience in identity and security. There are many issues like API security, authentication, data residency, privacy and compliance. Lee says that developers are implementing security much earlier in the process. This helps to explain the rise of social engineering attacks , especially with phishing.

NopSec
AUGUST 16, 2022
Critical Security Control 2: Inventory and Control of Software Assets SANS encourages companies to include authorized and unauthorized software in their IT asset inventory database. Critical Security Control 5: Account Management This control talks about the need to protect privileged user and administrative accounts.
Security Boulevard
MARCH 28, 2024
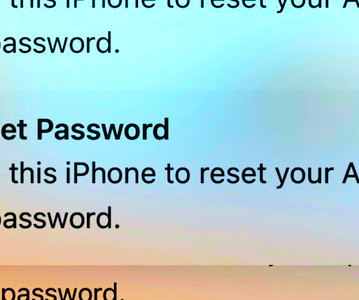
The post Apple OTP FAIL: ‘MFA Bomb’ Warning — Locks Accounts, Wipes iPhones appeared first on Security Boulevard. Rethink different: First, fatigue frightened users with multiple modal nighttime notifications. Next, call and pretend to be Apple support.

Security Boulevard
MAY 15, 2024
The post Dell Hell Redux — More Personal Info Stolen by ‘Menelik’ appeared first on Security Boulevard. Phish Ahoy! Hacker took advantage of Dell’s lack of anti-scraping defense.

Security Boulevard
MARCH 26, 2024
The post Telegram Privacy Nightmare: Don’t Opt In to P2PL appeared first on Security Boulevard. Scary SMS shenanigans: Avoid Telegram’s new “Peer-To-Peer Login” program if you value your privacy or your cellular service.

Security Through Education
DECEMBER 21, 2022
In October, Cybersecurity Awareness Month taught us the importance of safe practices such as the use of multifactor authentication, strong passwords, and VPNs. Only through learning about the tactic’s scammers use can we truly continue to improve our own personal security.

Spinone
MARCH 20, 2019
When considering a fully-featured and well thought out security plan , the human factor is an extremely important part of the equation, and arguably just as important as the technology component of the solution. In this article, we will take a look at cyber security awareness across an SMB organization.

Security Boulevard
JANUARY 18, 2024
The post Massive ‘New’ Leaked Credentials List: Naz.API Pwns Troy appeared first on Security Boulevard. Have I been pwned? Yes, you probably have. Stop reusing passwords, already. Here’s what else you should do.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content