9 Best Penetration Testing Tools for 2022
eSecurity Planet
FEBRUARY 24, 2022
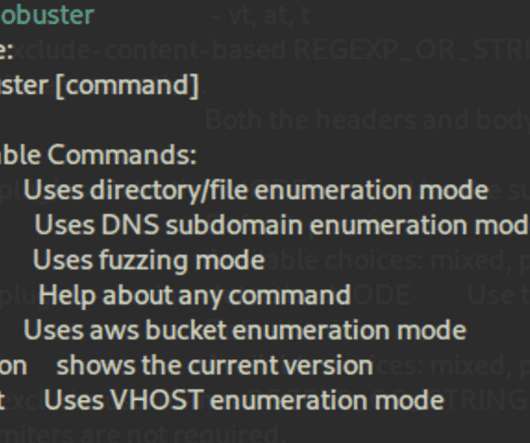
Can spot backup and configuration files. Great documentation. Lack of documentation. Nessus is a widely used paid vulnerability assessment tool that’s probably best for experienced security teams. Accepts Wordlists and additional packages ( sudo apt install seclists ). Can hide status and process (e.g.,














Let's personalize your content