LW ROUNDTABLE — How 2024’s cyber threats will transform the security landscape in 2025
The Last Watchdog
DECEMBER 16, 2024
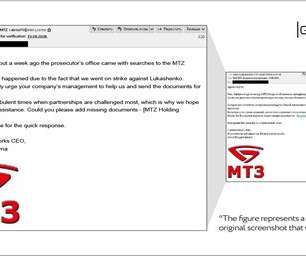
Continuing our look back at 2024, part two of Last Watchdogs year-ender roundtable turns its focus to emerging threats vs. evolving defense tactics. Part two of a four-part series The explosion of AI-driven phishing, insider threats, and business logic abuse has forced a shift toward more proactive, AI-enhanced defenses.
















































Let's personalize your content