Web Application Firewalls Adjust to Secure the Cloud
Dark Reading
JUNE 4, 2018
Cloud-based WAFs protect applications without the costs and complexity of on-prem hardware. Here's what to keep in mind as you browse the growing market.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 cloud-security web-application-firewalls-adjust-to-secure-the-cloud
cloud-security web-application-firewalls-adjust-to-secure-the-cloud 
Dark Reading
JUNE 4, 2018
Cloud-based WAFs protect applications without the costs and complexity of on-prem hardware. Here's what to keep in mind as you browse the growing market.

eSecurity Planet
DECEMBER 19, 2023
Infrastructure as a service security is a concept that assures the safety of organizations’ data, applications, and networks in the cloud. Understanding the risks, advantages, and best practices connected with IaaS security is becoming increasingly important as enterprises shift their infrastructure to the cloud.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

eSecurity Planet
OCTOBER 20, 2022
Cloud security builds off of the same IT infrastructure and security stack principles of a local data center. However, a cloud vendor offering provides a pre-packaged solution that absorbs some operational and security responsibilities from the customer. Shared Security Model: Cloud Provider Responsibilities.

CyberSecurity Insiders
APRIL 9, 2021
As we deploy more and more Web applications, we run the risk of overwhelming our security teams if we don’t give them the tools they need. Specifically, if your applications sit behind legacy web application firewall (WAF) technologies, the demands on your security team can quickly become unmanageable.

eSecurity Planet
FEBRUARY 13, 2024
Packet filtering is a firewall feature that allows or drops data packets based on simple, pre-defined rules regarding IP addresses, ports, or protocols. Once a type of firewall, packet filtering now provides a fundamental feature of nearly all firewalls and some network equipment (routers, smart switches, etc.).

eSecurity Planet
APRIL 30, 2024
Setting up a firewall is the first step in securing your network. A successful firewall setup and deployment requires careful design, implementation, and maintenance to effectively improve your network integrity and data security. Verify that the chosen firewall can meet your security standards and functions.

CyberSecurity Insiders
APRIL 6, 2021
Today’s business run on applications. So, if your organization is like most, you’re deploying more business-critical Web applications than ever before. However, as you scale up your use of web applications, you should take the time to reassess your approach to protecting those applications.

eSecurity Planet
FEBRUARY 14, 2024
Stateful inspection is a firewall feature that filters data packets based on the context of previous data packets. This important feature uses header information from established communication connections to improve overall security. Table of Contents Toggle How Does Stateful Inspection Work?

eSecurity Planet
SEPTEMBER 1, 2023
Cloud workload protection (CWP) is the process of monitoring and securing cloud workloads from threats, vulnerabilities, and unwanted access, and is typically accomplished via Cloud Workload Protection Platforms (CWPP). What Are the Challenges of Cloud Workload Protection?

eSecurity Planet
SEPTEMBER 10, 2021
From the very beginning of the cloud computing era, security has been the biggest concern among enterprises considering the public cloud. For many organizations, the idea of storing data or running applications on infrastructure that they do not manage directly seems inherently insecure. What is cloud security?
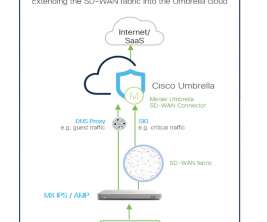
Cisco Security
MAY 17, 2021
It’s an exciting time in the world of networking and security. An unprecedented disruption is emerging in the way that we securely connect to resources and applications as well as the way that we consume these services. Which architecture should you choose for worldwide delivery of performant connectivity and top-notch security?

eSecurity Planet
AUGUST 22, 2023
Cybersecurity can be difficult to implement, and to make matters worse, the security professionals needed to do it right are in short supply. Managed IT security service providers (MSSPs) make life easier for organizations by providing outsourced expertise and tools at a fraction of the cost, time, and trouble of doing it yourself.

eSecurity Planet
APRIL 17, 2023
MetaAccess focuses on delivery of a virtual appliance that can be deployed with equal capability in local networks or in the cloud for robust, far-reaching capabilities. OPSWAT makes a variety of other products beyond NAC for application security, industrial cybersecurity, email security, malware analysis, zero trust access, and more.

Centraleyes
DECEMBER 25, 2023
However, the changing digital landscape, characterized by remote workforces, cloud-based applications, and interconnections with countless external systems, has shattered this once-solid paradigm. zero trust provides precisely that, ensuring that your security adapts to the evolving nature of your digital infrastructure.

Cisco Security
MARCH 16, 2021
Privacy and security are in constant tension. Along with others in the networking industry, we at Cisco are working to continually improve both security and privacy, without an advance in one area harming the other. As DoH becomes mainstream, a couple of changes are needed to maintain security. No snooping, no spoofing.

Centraleyes
JANUARY 4, 2024
Ignorance can be costly when safeguarding your cloud or hybrid networks. Today’s security teams face the challenge of monitoring the well-being and performance of a diverse array of on-premises and cloud applications, software, IoT devices, and remote networks. What is a Vulnerability Assessment?

eSecurity Planet
FEBRUARY 23, 2024
An application gateway, also known as an application level gateway (ALG), functions as a critical firewall proxy for network security. Its filtering capability ensures that only certain network application data is transmitted, which has an impact on the security of protocols including FTP, Telnet, RTSP, and BitTorrent.

eSecurity Planet
AUGUST 29, 2023
Firewall-as-a-Service (FWaaS) offers firewall capabilities as a cloud-based service. Traditional firewalls protect the network perimeter, enforcing security standards by regulating incoming and outgoing traffic according to rules and traffic analysis. Why Is There a Need for FWaaS?

eSecurity Planet
JUNE 21, 2022
An IT security certification can provide a key boost for your career, but with so many different certifications available (and so many organizations more than happy to take your money for training and testing), it’s important to make sure that the time and investment are well spent. How to Choose a Security Certification.

eSecurity Planet
NOVEMBER 22, 2023
Cloud security protects your critical information from unwanted access and potential threats through sophisticated procedures. Prioritizing cloud security helps guarantee that you have a safe, reliable resource for your data in today’s linked world. This increases user and service provider trust.

eSecurity Planet
OCTOBER 20, 2023
Hybrid cloud security is a framework for protecting data and applications in a computing environment that includes both private and public clouds. It combines on-premises and cloud-based resources to satisfy an organization’s diversified computing demands while ensuring strong security.

eSecurity Planet
APRIL 26, 2024
Network security architecture is a strategy that provides formal processes to design robust and secure networks. Effective implementation improves data throughput, system reliability, and overall security for any organization. or segregated as cloud or network attached storage (NAS).

eSecurity Planet
SEPTEMBER 3, 2022
Some overflow capacity or cloud-based scaling might be built into a robust system, but even these measures hit a technical or budgetary limit. Some overflow capacity or cloud-based scaling might be built into a robust system, but even these measures hit a technical or budgetary limit. Also read: How to Secure DNS. DDoS Recovery.

eSecurity Planet
DECEMBER 19, 2023
Cybercrime will go to the next level: Cyberattackers will implement improved skills, “shift left” attacks, and shifting strategies to adjust to evolving cyberdefense. Attack surfaces will explode: Cyberdefense complexity will compound as API, cloud, edge, and OT resources add to the list of assets to defend.

eSecurity Planet
OCTOBER 7, 2021
The network firewall is the first line of defense for traffic that passes in and out of a network. The firewall examines traffic to ensure it meets the security requirements set by the organization, and unauthorized access attempts are blocked. Firewall protection has come a long way in recent years. Firewall limitations.

eSecurity Planet
MAY 24, 2023
A cloud workload protection platform (CWPP) shields cloud workloads from a range of threats like malware, ransomware, DDoS attacks, cloud misconfigurations, insider threats, and data breaches.

eSecurity Planet
OCTOBER 26, 2023
Multi-cloud is a cloud computing strategy that enables businesses to run their applications and services across multiple private and public cloud platforms, so securing multi-cloud environments is a complicated task. Here is a step-by-step approach for making multi-cloud security work.

eSecurity Planet
JANUARY 30, 2024
Cloud storage security issues refer to the operational and functional challenges that organizations and consumers encounter when storing data in the cloud. Cloud storage risks involve potential external threats and vulnerabilities that jeopardize the security of stored data.

Security Boulevard
JUNE 23, 2023
Effective and proactive attack surface reduction strategies can complement your organization’s existing security measures to provide maximum protection against breach by minimizing the number of potentially vulnerable points in your network that cyber criminals can exploit.

eSecurity Planet
JANUARY 26, 2022
Network monitoring is where business performance meets cybersecurity , making it a critical component of any organization’s development, security, and operations ( DevSecOps ) pipeline. Monitoring network traffic across the hybrid IT environment in most organizations today is essential to proactive network management.

eSecurity Planet
NOVEMBER 18, 2022
Every IT environment and cybersecurity strategy has vulnerabilities. To avoid damage or loss, organizations need to find and eliminate those vulnerabilities before attackers can exploit them. Some of those vulnerabilities will be found and fixed by vendors, who will provide patches and updates for their products. How to Find Vulnerabilities.

CyberSecurity Insiders
DECEMBER 21, 2022
By Yaron Azerual, Senior Security Solution Lead, Radware. The reality is security teams need to rethink their approach to securing their APIs. THE STATE OF API SECURITY. The shift to hybrid working and digital transformation has accelerated the use of APIs. API attacks are largely undetected.

eSecurity Planet
NOVEMBER 3, 2022
Distributed denial of service (DDoS) attacks seek to cripple a corporate resource such as applications, web sites, servers, and routers, which can quickly lead to steep losses for victims. Another common problem is the discovery of weak authentication schemes such as Transport Layer Security (TLS) versions 1.0

eSecurity Planet
JUNE 23, 2022
Small businesses generally don’t have time to dip into logs several times a day, monitor every aspect of endpoint security via complex management consoles, or jump from point product to point product to stay on top of security. Best SMB Security Tools & Software. FortiGate Network Firewall. Key Differentiators.

eSecurity Planet
SEPTEMBER 26, 2023
FortSASE builds on Fortinet’s strong portfolio of security and networking tools to deliver a powerful option for secure access service edge (SASE) needs. Customers with existing Fortinet Gateways and other security products will benefit from the existing investment in appliances, configurations, and training. Who is Fortinet?

eSecurity Planet
MARCH 16, 2023
Network security threats weaken the defenses of an enterprise network, endangering proprietary data, critical applications, and the entire IT infrastructure. This guide to major network security threats covers detection methods as well as mitigation strategies for your organization to follow. Also read: What is Network Security?

eSecurity Planet
APRIL 13, 2022
In an age of strong data privacy laws like GDPR and CCPA , data loss prevention (DLP) technology is becoming a critically important IT security tool. Hiring, training, and retaining the staff needed to effectively run an information security program can be a challenge for any size business given the cybersecurity talent shortage.

eSecurity Planet
MARCH 28, 2023
Originally designed as a network access control (NAC) solution, Aruba ClearPass continues to evolve into a portfolio of network security tools. Applicable Metrics Aruba ClearPass is deployed in high-volume authentication environments (e.g. The company was founded in 2003 and is a wholly owned subsidiary of HPE. 30 points of presence).

eSecurity Planet
JUNE 20, 2023
However, it is extremely rare to locate this theoretical average company, and this average calculation hides the difference between different types of penetration testing (networks, applications, whole organizations, etc.) and different types of penetration tests (black box, gray box, white box, social engineering, etc.).

Cisco Security
AUGUST 28, 2023
The Black Hat Network Operations Center (NOC) provides a high security, high availability network in one of the most demanding environments in the world – the Black Hat event. We also provide integrated security, visibility and automation: a SOC (Security Operations Center) inside the NOC, with Grifter and Bart as the leaders.

Cisco Security
AUGUST 29, 2022
Port Security, by Ryan MacLennan, Ian Redden and Paul Fiddler. In technology, we plan as best as we can, execute tactically with the resources and knowledge we have at the time, focus on the strategic mission, adjust as the circumstances require, collaborate, and improve; with transparency and humility. The Buck Stops Here. Full stop.

eSecurity Planet
JANUARY 15, 2021
Having both the capabilities of detection and prevention are vital to effective security infrastructure. Prevention systems can adjust firewall rules on the fly to block or drop malicious traffic when it is detected but they do not have the robust identification capabilities of detection systems. Cloud compatible.

SecureList
DECEMBER 10, 2020
Organizations need to adapt to meet employee needs and ensure they stay productive, motivated and secure. The coronavirus pandemic has caused sudden, sweeping change around the world. The necessary social distancing measures are having an impact on all of us. What changed: guilty pleasures and life-work disbalance.

eSecurity Planet
MAY 27, 2021
With almost every aspect of business becoming more digital, enterprise network security software minimizes the impact of cyberattacks — especially as guarding against them protects a company’s operations and safeguards its competitiveness in a fast-moving marketplace. Top network security tools. Network Security Product.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content