CATSploit: An automated penetration testing tool
Penetration Testing
NOVEMBER 27, 2023
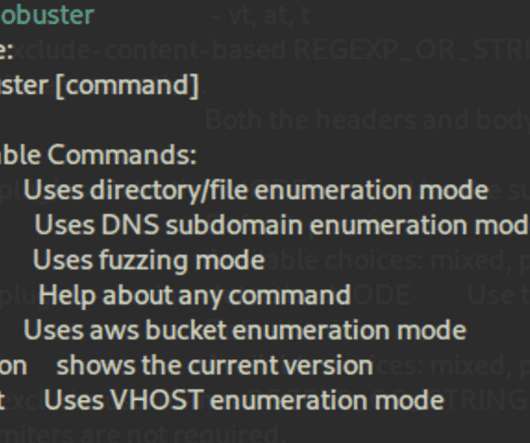
CATSploit CATSploit is an automated penetration testing tool using the Cyber Attack Techniques Scoring (CATS) method that can be used without a pentester.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Penetration Testing
NOVEMBER 27, 2023
CATSploit CATSploit is an automated penetration testing tool using the Cyber Attack Techniques Scoring (CATS) method that can be used without a pentester.
Appknox
AUGUST 7, 2022
Penetration Testing has become indispensable to most companies' secure software development lifecycle. Unfortunately, because of widespread misconceptions, several businesses still don't understand the true potential of pen testing and refrain from using it to ensure mobile app security. Penetration Testing Overview.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Boulevard
JANUARY 19, 2024
Penetration testing has become a cornerstone of robust cybersecurity strategy. It’s a critical process where experts simulate cyber attacks on your systems, networks, or applications to identify vulnerabilities before real.

Mitnick Security
OCTOBER 23, 2023
Penetration testing puts your security systems to the test so you can see if your security framework can withstand a cyber attack.

Mitnick Security
MARCH 3, 2023
Penetration testing is one such tool used to find the weaknesses in an organization’s cybersecurity measures. These cyber-attack simulations can either be done by software (automated penetration testing) or by cybersecurity experts known as pentesters (manual penetration testing).
Security Boulevard
APRIL 27, 2021
The most common news we hear in this digital era is regarding cyber-attacks. The post Test Your Detection Capabilities with Penetration Testing appeared first on Indusface. The post Test Your Detection Capabilities with Penetration Testing appeared first on Security Boulevard.

The Last Watchdog
FEBRUARY 24, 2022
Let us run you through the various aspects of penetration testing, or pen test, and why it is a critical component to protect a company’s network. A pen test is a simulated cyber attack on your systems to identify the loopholes that hackers can exploit. Are they updated? Are the credentials updated?
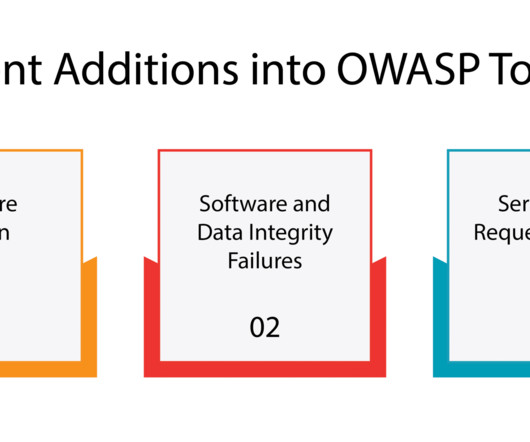
Security Boulevard
MAY 2, 2023
The Open Web Application Security Project (OWASP) is an online community that was established on September 9, 2001, by Mark Curphey, a cybersecurity expert, with the objective of mitigating cyber attacks. OWASP has developed a list of the top 10 […] The post OWASP Penetration Testing: Your Ultimate Guide!

eSecurity Planet
MARCH 7, 2023
Penetration tests are simulated cyber attacks executed by white hat hackers on systems and networks. The goal of these simulations is to detect vulnerabilities, misconfigurations, errors, and other weaknesses that real attackers could exploit. However, they are also the most realistic tests.
Penetration Testing
JANUARY 31, 2024
This intrusion was notable for its utilization of a variety of open-source tools... The post Decoding REF0657: A Sophisticated Financial Cyber Attack Exposed appeared first on Penetration Testing.

Penetration Testing
NOVEMBER 28, 2023
In a concerning turn of events, DP World Australia, one of Australia’s largest port operators, has disclosed that a recent cyber attack resulted in unauthorized access to employee data.
eSecurity Planet
FEBRUARY 24, 2022
A penetration test , or pen test, is the simulation of a cyber attack. This critical IT security practice isn’t the same as a vulnerability assessment or vulnerability scanning, though, as pen testing involves an actual attack similar to what hackers would do in real-world conditions.

Penetration Testing
NOVEMBER 9, 2023
Today, the Financial Times reported that the American branch of the Industrial and Commercial Bank of China has suffered a cyber attack, resulting in the bank’s inability to settle a substantial volume of transactions....
Mitnick Security
APRIL 4, 2024
You may be surprised to learn that while Apple devices are typically perceived as safer than Windows-based PCs, they are far from impervious to cyber attacks. Powering your business with Apple devices because of their reputable security and privacy features?

CyberSecurity Insiders
JUNE 3, 2021
Businesses are venturing into using automated penetration testing to replace or complement their conventional cyber threat assessments. It’s no surprise, considering how time-consuming and tedious running manual pen tests can be. But first… What is automated penetration testing?

Mitnick Security
SEPTEMBER 2, 2022
Penetration testing — a simulated cyber attack performed by experts — is crucial when it comes to assessing your network’s vulnerabilities. There are several steps you can take to protect your organization from threat actors, but how do you know if your cybersecurity posture is strong enough?

Penetration Testing
DECEMBER 4, 2023
The Kaspersky Security Bulletin 2023 offers a comprehensive overview of this ever-changing digital environment, providing key insights... The post Kaspersky Report Reveals Alarming Surge in Cyber Attacks appeared first on Penetration Testing.

Pen Test
OCTOBER 12, 2023
Introduction Radio Frequency (RF) penetration testing, popularly referred to as RF pentesting, stands as a vital domain within ethical hacking. In the contemporary digital era, Radio Frequency (RF) penetration testing, commonly known as RF pentesting, is indispensable due to several pivotal factors that underscore its significance.

Penetration Testing
JANUARY 17, 2024
In a recent revelation, Microsoft has uncovered a concerning cyber-espionage campaign conducted by Mint Sandstorm, a notorious threat actor group with links to the Islamic Revolutionary Guard Corps (IRGC) of Iran’s military.

Mitnick Security
JUNE 27, 2023
According to Cybersecurity Magazine, 60% of small businesses go out of business within six months of falling victim to a data breach or cyber attack. As a Chief Information Security Officer (CISO), you have the responsibility of not only directing your organization’s security but also conveying your risk status to leadership.
Appknox
APRIL 17, 2023
However, we must also be cautious of its darker side - the looming risk of cyber attacks. With just a few clicks, one can engage in commerce, establish a virtual hub for their services, leverage cloud technology, advertise on a massive scale, and so much more.

Penetration Testing
NOVEMBER 22, 2023
Experts from VMware Carbon Black are sounding the alarm: there has been a recent uptick in cyber attacks targeting the educational sector, government institutions, and service industry enterprises.
Penetration Testing
APRIL 15, 2024
Recently, the notorious TA558 group has escalated its offensive, orchestrating a sophisticated series of cyber attacks targeting an array of institutions and companies worldwide.

Penetration Testing
APRIL 5, 2024
This powerful tool is designed to enhance security by identifying and detecting various types of cyber attacks within your... The post OSTE-Web-Log-Analyzer: automate the process of analyzing web server logs appeared first on Penetration Testing.

Penetration Testing
JANUARY 18, 2024
In a recent discovery, Varonis Threat Labs has unveiled three new ways that cyber attackers can exploit to access NTLM v2 hashed passwords, putting countless systems and user data at risk.

Security Boulevard
APRIL 25, 2024
With cyber threats constantly evolving, protecting your network’s security is important. Network pen testing, also known as Network VAPT (Vulnerability Assessment and Penetration Testing), helps you attain this objective. Network infrastructure […] The post What is Network Pen Testing?

NopSec
AUGUST 9, 2022
Once you’ve started a vulnerability scanning system , you may want to take the next step in identifying vulnerabilities: penetration testing, commonly referred to as pentesting. The Basics of Penetration Testing Pentesting can be as broad or narrow as the client wishes. This more closely simulates an actual cyber attack.

Penetration Testing
JANUARY 11, 2024
Recently, Forcepoint X-Labs, a vanguard in cybersecurity, has unveiled an intricate cyber-attack targeting business leaders during a pivotal general election period.

Penetration Testing
JANUARY 19, 2024
In an unprecedented turn of events, Microsoft’s security team has recently unearthed an insidious cyber attack, carried out by the notorious Russian state-sponsored actor known as Midnight Blizzard, or Nobelium.

Penetration Testing
DECEMBER 26, 2023
In the vast expanse of the digital ocean, a new wave of cyber attacks has emerged, targeting the seemingly unassuming Linux SSH servers.

Penetration Testing
JANUARY 16, 2024
In 2023, the world faced an unprecedented surge in cyber threats, a storm that Check Point Research’s analysis has vividly captured. The year marked a new high in cyber attacks, with a 1% increase... The post Ransomware Surge: 1 in 10 Organizations Targeted Globally in 2023 appeared first on Penetration Testing.

Penetration Testing
DECEMBER 11, 2023
This group, known for its meticulous cyber attacks on Ukrainian electric utilities, represents a new era of cyber... The post Unmasking ELECTRUM: Cyber Predators of the Ukrainian Grid appeared first on Penetration Testing.

Penetration Testing
DECEMBER 5, 2023
As the digital landscape evolves, so does the nature of cyber threats. 2023 witnessed a significant shift in the tactics and approaches of cyber attackers, influenced by global conflicts and advancements in technology.

Penetration Testing
DECEMBER 1, 2023
In a groundbreaking discovery, researchers from Unit 42 at Palo Alto Networks have uncovered a new toolset being used in cyber attacks against organizations in the Middle East, Africa, and the United States.

Penetration Testing
JANUARY 18, 2024
After a mysterious nine-month hiatus, the digital underworld witnessed the reemergence of TA866, a formidable threat in the realm of email-based cyber-attacks.

Penetration Testing
NOVEMBER 13, 2023
The latest victim in a series of cyber-attacks targeting... The post Bitcoin ATM Company Coin Cloud Suffers Massive Data Breach, Exposing Personal Information of 300,000 Customers appeared first on Penetration Testing.

Penetration Testing
DECEMBER 7, 2023
Cybersecurity and Infrastructure Security Agency (CISA) unraveled a cyber attack that not only breached technological defenses but also posed a threat to public safety. This incident involved the active... The post Hackers attacked US water facility via CVE-2023-6448 vulnerability appeared first on Penetration Testing.

Penetration Testing
JANUARY 3, 2024
In the ever-evolving landscape of cyber threats, a new contender with a sophisticated approach to digital espionage has emerged.

Penetration Testing
NOVEMBER 29, 2023
In the ever-evolving landscape of cyber threats, a new formidable player has emerged: the FlowerPower APT campaign.

eSecurity Planet
OCTOBER 13, 2023
Penetration testing is a critically important cybersecurity practice, but one that many organizations lack the on-staff skills to do themselves. Fortunately, there are many pentesting services out there that can do the job for them across a range of budgets and needs.

The Last Watchdog
JULY 15, 2019
Cyber crime can be extremely financially damaging to businesses. However, if you believe that money is the only thing that a cyber-attack costs your organization, you would be wrong. In fact, a recent academic analysis identified 57 specific individual negative factors that result from a cyber-attack against a business.

Appknox
DECEMBER 8, 2021
Stats suggest that 43% of cyber attacks target small businesses and 60% of these attacks are encountered within the first 6 months of setting up a business.

Security Boulevard
JANUARY 30, 2023
Red teaming is a simulated cyber attack that assesses an organization's security by having security professionals act as pseudo-hackers to identify and exploit vulnerabilities. appeared first on Penetration Testing UK - Sencode. The post What is Red Teaming? appeared first on Security Boulevard.

Penetration Testing
DECEMBER 21, 2023
At the heart of... The post Beyond Breaches: 2024’s Cyber War – Extortion, Manipulation, and New Battlegrounds appeared first on Penetration Testing. Resecurity’s insightful forecast for 2024 paints a vivid picture of the challenges that lie ahead.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content