The Future of Privacy: How Big Tech Is Changing the Way We Think About Our Data
Cytelligence
DECEMBER 8, 2023
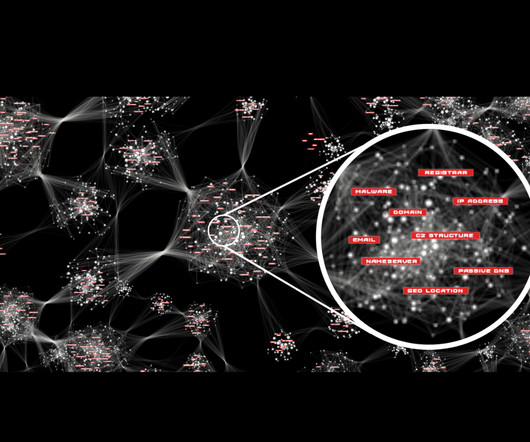
Major cybersecurity corporations specializing in services such as cybersecurity audits, vulnerability assessments, and ransomware consulting play a critical role in fortifying defenses against cyber threats, including ransomware attacks. The impact of Big Tech on privacy is multifaceted.





















Let's personalize your content