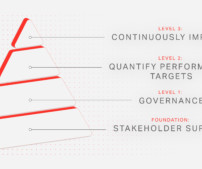
Forging the Path to Continuous Audit Readiness
CyberSecurity Insiders
JANUARY 9, 2023
Technology oversight is a common mandate across IT and security frameworks and compliance specifications, but achieving that oversight is difficult. The rise of hybrid workplaces, shadow IT/DevOps, and cloud infrastructure dynamics continue to create cybersecurity risks. 1 ESG Research: 2021: State of Data Privacy and Compliance.
















Let's personalize your content