Evolving VPN giant: CyberGhost Acquired PIA [2019]
SecureBlitz
APRIL 11, 2024
The winds of change are blowing in the world of virtual private networks (VPNs).
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

SecureBlitz
APRIL 11, 2024
The winds of change are blowing in the world of virtual private networks (VPNs).

CyberSecurity Insiders
AUGUST 6, 2021
According to most studies, most people use VPNs for personal reasons instead of using them for business purposes alone. VPNs allow tremendous liberty when it comes to network and data protection and, as such, are necessary for every internet consumer, business, and entertainment alike. Faster internet speed.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
SecureBlitz
NOVEMBER 12, 2021
In this post, we will show you what a VPN is all about. You will also identify the VPN features and benefits. Before we proceed, you need to know what VPN is all about. What Is A VPN? Virtual Private Network (VPN) is a technology that cloaks a digital device across the internet and enables.

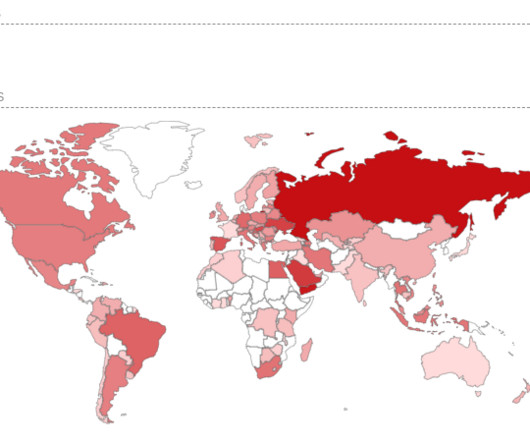
Joseph Steinberg
MAY 9, 2022
According to a report published by The Washington Post , downloads by Russians of the 10 most popular VPN applications jumped from fewer than 15,000 per day just before the Russian invasion of Ukraine to a current figure of over 300,000 a day – even reaching as high as 475,000 per day at one point during the current military campaign.

Adam Levin
MARCH 19, 2020
With businesses sending employees to work from home in the wake of Covid-19, the cybersecurity of their home offices has become paramount. Here are five ways VPNs can keep remote employees secure. You Can Restrict Access To Company Data: Restricting access to a VPN to current employees means it’s easier to spot a usage anomaly.

Approachable Cyber Threats
SEPTEMBER 30, 2021
Category Cybersecurity Fundamentals Risk Level. You can’t access that app someone mentioned, so you ask them and they tell you to “just use the VPN.” And why can you access the app after using the VPN, but you couldn’t before? This is where a VPN comes in. What does that mean? But can we back up first?”

Javvad Malik
NOVEMBER 1, 2021
Like many people, over the last couple of years, my main real interaction with people outside of my immediate family and Amazon delivery drivers has been via the internet. The beauty of the internet is that you don’t need to shower, put on decent clothes, or worry about offending anyone. I may be slightly jealous of Dan Cuthbert ).

The Last Watchdog
DECEMBER 14, 2023
Here’s part two of Last Watchdog’s year-end tête-à-tête with top cybersecurity experts. Instead of arguing about MFA strength, VPN vendor, or nation-state treat actors, let’s finish our conversation about using dedicated administrator accounts and unique passwords. AI is set to completely transform cybersecurity.

The Last Watchdog
JULY 11, 2022
It’s in findings of a deep dive data analytics study led by Surfshark , a supplier of VPN services aimed at the consumer and SMB markets. Surfshark partnered with a number of independent cybersecurity researchers to quantify the scope and pattern of data breaches over the past couple of decades. Essential security tool.

IT Security Guru
MARCH 21, 2023
As information technology continues to evolve, more and more people are penetrating cyberspace. But is it always safe to surf the internet? How Does Immersive Technology Affect Cybersecurity? That is why it is important to ensure safety on multiple devices with a VPN.

Malwarebytes
FEBRUARY 27, 2021
VPNs have been a subject of deliberation for a long time. I think the pandemic has made it clear that, yes, using a VPN is useful, even necessary, most especially for those working remotely. We’re going to take a look at free VPNs and paid VPNs in general. The honest free VPN. The mystery free VPN.
Krebs on Security
JUNE 15, 2023
government agency in charge of improving the nation’s cybersecurity posture is ordering all federal agencies to take new measures to restrict access to Internet-exposed networking equipment. “This is reachable pre-authentication, on every SSL VPN appliance,” French vulnerability researcher Charles Fol tweeted.

The Last Watchdog
OCTOBER 24, 2022
In addition, educating employees about cybersecurity issues can help to reinforce the security-minded culture of the organization and change employee behaviour. Training employees is a crucial part of fighting back against this kind of attack and can complement other technological security solutions. Use a corporate VPN.

SecureWorld News
JANUARY 21, 2024
Battling cybersecurity threats can often feel like an uphill struggle. Let's take a closer look at some key cybersecurity strategies for nonprofits to consider. Let's take a closer look at some key cybersecurity strategies for nonprofits to consider.

Tech Republic Security
MAY 13, 2020
With the shift toward remote working, cybercriminals have been targeting exploits in VPN, Internet of Things, and authentication technology, says cybersecurity firm Nuspire.

Adam Levin
NOVEMBER 15, 2019
News that Virtual Private Network ( VPN ) provider NordVPN was breached spread quickly. While the breach of a major VPN service is newsworthy, this one wasn’t particularly. But one of the watchwords of good cyber hygiene, a VPN, was breached. Who Is Using VPNs? The incident put NordVPN in the hot seat.

Security Affairs
FEBRUARY 16, 2024
Cybersecurity and Infrastructure Security Agency (CISA) revealed that a threat actor gained access to an unnamed state government organization’s network environment via an administrator account belonging to a former employee. ” reads the report published by CISA. CISA did not attribute the attack to a specific threat actor.

eSecurity Planet
JULY 3, 2021
The internet and, now, cloud computing transformed the way we conduct business. Enter VPN technology. One longtime cybersecurity solution for small teams up to global enterprise networks is virtual private networks (VPN). Top VPN products. CyberGhost VPN. The CyberGhost VPN app has an average 4.1/5

The Last Watchdog
MAY 23, 2022
Then the Internet took off and trusting the connection between a user’s device and a web server became of paramount importance. This challenge has not escaped the global cybersecurity community. I had the chance to talk about DigiCert’s perspective with Jason Sabin, DigiCert’s Chief Technology Officer. Trust under siege.

Krebs on Security
DECEMBER 2, 2021
In January 2021, technology vendor Ubiquiti Inc. Federal prosecutors say Nickolas Sharp , a senior developer at Ubiquiti, actually caused the “breach” that forced Ubiquiti to disclose a cybersecurity incident in January. The message was sent through an IP address associated with the same Surfshark VPN.

Security Boulevard
FEBRUARY 2, 2024
Introduction Ivanti, an IT management and security company, has issued a warning about multiple zero-day vulnerabilities in its VPN products exploited by Chinese state-backed hackers since December 2023. to gain access to ICS VPN appliances. to gain access to ICS VPN appliances.

Security Affairs
APRIL 26, 2019
One in four internet users use a VPN regularly, but how much does the average user know about what goes on behind the software? Pulling back the curtain, a VPN runs on various VPN protocols that govern the way a VPN client communicates with a VPN server. IKEv2 is uniquely suited to mobile VPN solutions.

Malwarebytes
JULY 28, 2021
Researchers at RandoriSec have found serious vulnerabilities in the firmware provided by UDP Technology to Geutebrück and many other IP camera vendors. According to the researchers the firmware supplier UDP Technology fails to respond to their reports despite numerous mails and LinkedIn messages.

The Last Watchdog
MARCH 6, 2021
Technology advancements have made it relatively easy for many employees to carry out their regular job duties from the comfort of their home. Your employers might be able to provide you with specific directions on how to handle certain aspects of your cybersecurity. Related: Poll confirms rise of Covid 19-related hacks.
Security Affairs
MAY 24, 2024
The use of Dynamic DNS (DDNS) services embedded in appliances, such as those provided by vendors like Fortinet or QNAP, carries cybersecurity implications. Threat scenario The use of Dynamic DNS (DDNS [1] ) services embedded in appliances, such as those provided by vendors like Fortinet or QNAP, carries cybersecurity implications.

eSecurity Planet
MAY 2, 2024
The 2023 vendor surveys arriving this quarter paint a picture of a cybersecurity landscape under attack, with priority issues affecting deployment, alert response, and exposed vulnerabilities. This article details two major findings from the report: five major cybersecurity threats and prioritization problems.

The Last Watchdog
DECEMBER 13, 2021
Privacy and cybersecurity challenges and controversies reverberated through all aspect of business, government and culture in the year coming to a close. Related: Thumbs up for Biden’s cybersecurity exec order. Sascha Fahrbach , cybersecurity evangelist, Fudo Security. There are 550+ known CVEs targeting VPN today.

CyberSecurity Insiders
SEPTEMBER 24, 2021
Today, technological advances have seen a rise in cyber security threats globally. Besides, cybercriminals are becoming craftier with sophisticated technology. This article discusses top areas in IT where you need to strengthen cybersecurity measures to avoid data breaches and information loss: Networks. Human Resources.

SecureWorld News
FEBRUARY 24, 2022
For months now, cybersecurity professionals have witnessed the increased aggression of malicious Russian cyber activity as the country amassed tens of thousands of troops at the Ukraine border. When Russian troops launched an assault on multiple Ukrainian cities last night, the cybersecurity community was ready to respond.

eSecurity Planet
APRIL 26, 2022
Achieving funding is no simple task, and cybersecurity entrepreneurs have a difficult path competing in a complex and competitive landscape. Luckily for cybersecurity startups, there’s no shortage of interest in tomorrow’s next big security vendors. Investments in cybersecurity more than doubled from $12 billion to $29.5

CyberSecurity Insiders
MARCH 21, 2021
With a VPN like Surfshark to encrypt your online traffic and keep it protected against any security breach, your valuable data isn’t going to get compromised easily anytime soon. Most small business owners consider IP infrastructure as a one-time expense and dont bother replacing it with new technology. Build a cyber security plan .

Adam Levin
JANUARY 2, 2019
2019 will be the year consumers start thinking more about cyber hygiene , and the year Congress becomes more proactive in the areas of privacy and cybersecurity. We can expect even more competition in this area from other major technology players. The post Will 2019 Be the Year Cybersecurity Goes Mainstream?

Approachable Cyber Threats
OCTOBER 16, 2020
Back in June, the Department of Homeland Security (DHS) issued an advisory that married together two of today’s major cybersecurity concerns: remote access technology and ransomware. Generally speaking, this is any technology that lets you access your organization’s IT resources while you’re away from the office.

CyberSecurity Insiders
JUNE 7, 2023
Therefore, it’s crucial that small businesses make cybersecurity a top priority. What drives more cybersecurity attacks on small businesses? The influx of remote working culture has added new challenges and cybersecurity risks for small businesses. They also have a limited budget to spend on effective cyber security measures.

Security Affairs
JUNE 19, 2021
North Korea-linked APT group Kimsuky allegedly breached South Korea’s atomic research agency KAERI by exploiting a VPN vulnerability. The investigation into the intrusion revealed the involvement of 13 internet addresses including one traced to the Kimsuky APt group. ” reported the Reuters. ” reported The Record.

Krebs on Security
NOVEMBER 21, 2020
NiceHash founder Matjaz Skorjanc said the unauthorized changes were made from an Internet address at GoDaddy, and that the attackers tried to use their access to its incoming NiceHash emails to perform password resets on various third-party services, including Slack and Github.

eSecurity Planet
MAY 28, 2024
Security service edge (SSE) is a security technology that secures access to assets outside of the corporate network. Improved Remote Security Remote users often bypass VPN security to directly access cloud apps such as Office 365 and Salesforce or to browse the web.

Joseph Steinberg
JULY 17, 2023
Don’t assume that because security technology is available to address a particular danger, and an organization utilizes such technology, that the organization is actually secure against that particular danger. The technology to prevent errors of the “ML” vs “MIL” type has been around for many years.

IT Security Guru
MARCH 28, 2023
However, in all this fuss and mess, cybersecurity issues increased. Yes, cybersecurity has become a major concern, and sadly, it’s still overlooked. Let’s talk about the significance of cybersecurity today and see how you can increase data security and privacy. Why is Cybersecurity Important?

The Last Watchdog
JUNE 4, 2019
With the largest concentration of cybersecurity expertise –– the “oil” — in the world, Maryland is fast changing from the Old Line State into “Cybersecurity Valley.” In Silicon Valley, the initial technology seeds were planted in World War II, when the U.S. There’s oil in the state of Maryland – “cyber oil.”
IT Security Guru
NOVEMBER 11, 2021
Operational technology (OT) used to be the specialist networks nobody in IT bothered with, or perhaps thought they didn’t need to. Organisations, and increasingly regulators, must now live with the implications of this for cybersecurity. If someone compromised a VPN, they could basically go anywhere on that network.”.
Security Affairs
FEBRUARY 4, 2024
Clorox estimates the costs of the August cyberattack will exceed $49 Million Mastodon fixed a flaw that can allow the takeover of any account Iranian hackers breached Albania’s Institute of Statistics (INSTAT) Operation Synergia led to the arrest of 31 individuals Ex CIA employee Joshua Adam Schulte sentenced to 40 years in prison Cloudflare breached (..)

SecureWorld News
FEBRUARY 9, 2024
People, process & technology framework A successful IAM program requires all three dimensions—people, process, and technology—working in concert to enhance the user experience, fuel efficiency gains, and minimize enterprise risk. Self-Sovereign Identity (SSI) is a bold new frontier in identity and access management (IAM).

SecureWorld News
APRIL 15, 2021
And the administration also names Russia as the bad actor behind other documented IT and cybersecurity tool attacks. Today, the National Security Agency, the Cybersecurity & Infrastructure Security Agency, and the Federal Bureau of Investigation are jointly issuing a cybersecurity advisory, 'Russian SVR Targets U.S.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content