The Vulnerability Lag: Cut Ransomware Risks Resulting From Digital Transformation
Dark Reading
DECEMBER 10, 2021
Exploring ransomware and other data integrity risks from accelerated digital transformation in the wake of COVID-19.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Dark Reading
DECEMBER 10, 2021
Exploring ransomware and other data integrity risks from accelerated digital transformation in the wake of COVID-19.
Security Boulevard
APRIL 14, 2021
Digital Resilience is the New Digital Transformation KPI. Innovation and digital transformation rely on digital resilience to turn business disruption into revenue opportunities. What is Digital Resilience? Digital resilience was a major theme at IDC Directions 2021 in March. Sharon Bell.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Tech Republic Security
JULY 24, 2022
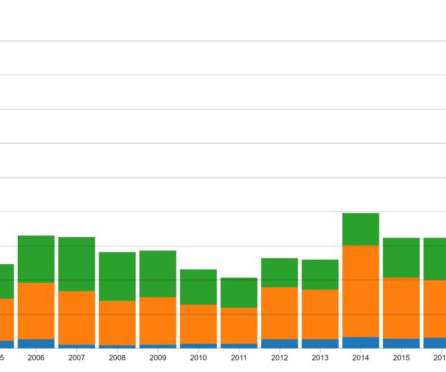
Not to mention the negative financial impacts and reputational damage that ransomware can cause. The overall frequency of ransomware detections might be leveling off, but the sophistication, aggressiveness, and impact of this threat continues relentlessly.

The Last Watchdog
MAY 31, 2022
Related: Log4J’s long-run risks. Advanced VM tools and practices are rapidly emerging to help companies mitigate a sprawling array of security flaws spinning out of digital transformation. It supplies a unified vulnerability and risk management solution that automates vulnerability management processes and workflows.

Tech Republic Security
JULY 24, 2022
The post Top Four Steps to Reduce Ransomware Risk appeared first on TechRepublic. IT leaders must integrate security tools into a cooperative, consolidated ecosystem using a composable and scalable cybersecurity mesh architecture (CSMA) approach. By 2024, organizations adopting a CSMA to integrate security tools to.

CyberSecurity Insiders
FEBRUARY 16, 2021
2021 Research Highlights Growing Security Vulnerabilities Around Targeted Social Engineering, Ransomware and Malware Attacks. To download the full study, see the Zscaler 2021 VPN Risk Report. The full findings of the Zscaler VPN Risk Report are now available to the public. Zscaler, Inc. About Zscaler. Media Contacts.

Security Boulevard
OCTOBER 20, 2022
Time to Accept the Risk of Open Source? Where is the real risk? Accepting Open Source Risk. Accepting cybersecurity risk has become the norm for organizations. Artificial intelligence, machine learning, blockchain, and quantum computing reduce risk. What is the True Risk of Open-source Libraries?

CyberSecurity Insiders
JUNE 7, 2023
Here are three risk mitigation imperatives that can help organizations get a better handle on these latest risks and threats. The latest bill to address data threats is the RESTRICT Act , also known as the Restricting the Emergence of Security Threats that Risk Information and Communications Technology Act.

Tech Republic Security
JULY 24, 2022
Increasingly, these cybercriminals are doing more than stealing data, often encrypting whole systems and interrupting business operations with ransomware, a threat that’s increased 15x over the past. The post Reduce Ransomware Risk With the Fortinet Security Fabric appeared first on TechRepublic.

Jane Frankland
APRIL 17, 2024
Without upholding digital trust, with every click, we not only risk security breaches, fraud and the misuse of our data but one’s own company’s reputation and the very foundation of our business operations. This makes sense, especially considering the relationship between trust, digital transformations and cybersecurity.

Security Boulevard
DECEMBER 6, 2023
Taking a Proactive Approach to Mitigating Ransomware Part 1: You Can’t Neglect the Application Layer ltabo Wed, 12/06/2023 - 18:42 Ransomware continues to dominate cybersecurity news. Recovery costs for ransomware attacks have also continued to increase year-over-year, up 30% from 2022 to 2023.

SecureWorld News
DECEMBER 24, 2021
The library has digitized approximately 25% of its documents so far. Manilo Miceli, the Chief Information Officer of the library, told The Guardian this transition comes with risk. "We We cannot ignore that our digital infrastructure is of interest to hackers. This project is about a lot more than just physical preservation.

SecureWorld News
NOVEMBER 12, 2020
The library has digitized approximately 25% of their documents so far. Manilo Miceli, the Chief Information Officer of the library, told The Guardian this transition comes with risk. "We We cannot ignore that our digital infrastructure is of interest to hackers. This project is about a lot more than just physical preservation.

Malwarebytes
FEBRUARY 7, 2023
ION Group, a financial software firm, is reportedly beginning to bring clients back online after being hit by a ransomware attack late last week. The Russian-linked LockBit ransomware group claimed responsibility for attacking a division of ION Group, which affecting 42 clients in Europe and the United States. Get an EDR solution.

Security Boulevard
JULY 7, 2022
Risks to Your Network from Insecure Code Signing Processes. However, this practice puts these critical resources at risk for being misused or compromised. However, InfoSec teams need to understand that significant risks exist around poor code signing hygiene. brooke.crothers. Thu, 07/07/2022 - 15:26. Private key sprawl.

SC Magazine
JULY 13, 2021
News of the breach was first reported by BleepingComputer on Monday, though DataBreaches.net had previously reported that the DarkSide ransomware group had listed Guess on their data leak site in April. It’s certainly possible that the reported ransomware and breach incidents may be linked.

Security Boulevard
SEPTEMBER 27, 2022
2022 began with successful ransomware attacks against global IT and digital transformation providers, no thanks to the notorious LAPSUS$ ransomware gang. Often, any discussion about ransomware impact has mostly centered on affected organizations.
eSecurity Planet
JANUARY 6, 2022
Third-party security, ransomware , artificial intelligence (AI) and decentralized finance (DeFi) are some of the threats you can expect to see more of this year – with the potential for far worse results than we’ve seen in the past. Third-party Risks Take Center Stage. Ransomware and Critical Infrastructure Attacks Get Worse.

Security Boulevard
DECEMBER 5, 2022
Dubbed CryWiper, it pretends to be ransomware. The post Russia Hit by New ‘CryWiper’ — Fake Ransomware appeared first on Security Boulevard. A new wiper malware is destroying data on Russian government PCs.
CyberSecurity Insiders
DECEMBER 14, 2021
INDIANAPOLIS–( BUSINESS WIRE )– Pondurance , a leader in Managed Detection and Response (MDR) services, today launched Cyber Risk Assessments powered by MyCyberScorecard. Comprehensive views of low, medium and high risk MyCyberScores. Streamlined workflows and robust analytics.

IT Security Guru
JULY 19, 2021
Although cybercrime as a whole has seen a rise during the pandemic, arguably ransomware has been one of the more successful and lucrative attack types. Our own research report, the State of Encrypted Attacks Report 2020 , found that there had been a 500 per cent rise in ransomware compared to 2019. Security hygiene is the best defence.

The Last Watchdog
DECEMBER 19, 2022
Related: IABs fuel ransomware surge. The rise of IABs corresponds with the increase in digital transformation. Early in the COVID-19 pandemic, companies started implementing digital tools at an unprecedented pace. Ransomware correlation. As IABs continue to grow, so will ransomware. Mitigating IABs.

The Last Watchdog
JANUARY 29, 2023
Ransomware is at an all-time high; attackers are as elusive as ever. CSOs and CISOs, need to be able to convey the risks that their teams face, especially to board members who can easily get lost in explanations of the endless technical nuances. Digital transformation affecting security. The threat of ransomware.

The Last Watchdog
MAY 12, 2021
A new report from Sophos dissects how hackers spent two weeks roaming far-and-wide through the modern network of a large enterprise getting into a prime position to carry out what could’ve been a devasting ransomware attack. They used very nation state-like tactics, from a ransomware perspective,” Schiappa told me.

Thales Cloud Protection & Licensing
MAY 8, 2023
Thales 2023 Data Threat Report: Sovereignty, Transformation, and Global Challenges madhav Tue, 05/09/2023 - 05:30 Despite the economic and geopolitical instability in 2022, enterprises continued to invest in their operations and digital transformation. Risk awareness is rising Risk awareness rises together with cloud adoption.

CyberSecurity Insiders
SEPTEMBER 27, 2021
Given how critical security is to digital transformation and our ability to innovate, we’ve got a robust line-up of cybersecurity topics – from SASE to zero trust and the technologies you need to help protect your business. And it’s jam-packed with cybersecurity talks! Speaker: Rupesh Chokshi.

The Last Watchdog
MAY 18, 2022
I sat down with Erkang Zheng, founder and CEO of JupiterOne , a Morrisville, NC-based CAASM platform provider, to discuss how security got left so far behind in digital transformation – and why getting attack surface management under control is an essential first step to catching up. But then along came digital transformation.

SecureWorld News
JULY 22, 2021
One of the sessions, Find and Fix Your Security Blind Spot, presented by industry leader Gigamon, looks at how the rapid digital transformation has overwhelmed IT teams with broader and new attack surfaces. The opening keynote, Ransomware: Today's Cyber Weapon of Choice, presented by CNN Military Analyst and cyber thought leader Col.

The Security Ledger
JULY 22, 2020
In this Spotlight podcast* we’re joined by Andrew Jaquith, the CISO at QOMPLX to talk about how the COVID pandemic is highlighting longstanding problems with cyber risk management and cyber resilience. We also talk about how better instrumenting of information security can help companies get a grip on fast-evolving cyber risks like.

Thales Cloud Protection & Licensing
APRIL 29, 2024
It fuels innovation, drives customer loyalty, and underpins successful digital transformation. The Thales 2024 Trust Index report indicates that 87% of consumers expect vendors to respect their digital rights, which leads to trusted relationships. to streamline processes and enhance digital trust in their customer interactions.

IT Security Guru
FEBRUARY 28, 2022
Given the connectivity needs of a remote workforce – and knowing a hybrid workforce is here to stay – many IT teams have had to make sudden changes in the way workers connect to corporate systems that could introduce new cyber risks and vulnerabilities. . Either way, they are more devious and better equipped than 12 months ago.

The Security Ledger
AUGUST 28, 2020
Given the magnitude of the problem, could taking a more risk-based approach to security pay off? Given the magnitude of the problem, could taking a more risk-based approach to security pay off? A Risk Eye on the Election Guy. Read the whole entry. » What does such an approach look like?

Security Boulevard
APRIL 29, 2024
It fuels innovation, drives customer loyalty, and underpins successful digital transformation. The Thales 2024 Trust Index report indicates that 87% of consumers expect vendors to respect their digital rights, which leads to trusted relationships. to streamline processes and enhance digital trust in their customer interactions.

NetSpi Executives
JANUARY 8, 2024
From the emergence of the MOVEit vulnerability to the wide adoption of ChatGPT and its associated security risks, nearly every industry was impacted by cyber threats. Teams must keep pace with digital transformation to ensure cloud security. The past year certainly had no shortage of cybersecurity firsts.

Herjavec Group
DECEMBER 16, 2020
At the onset of the year, we predicted that the top priority for any CISO or CIO will be to manage the risk associated with digital transformation and enhance their security programs in order to keep up with new technological complexity. Sophisticated Ransomware . Looking back, that was an understatement! .

Security Boulevard
AUGUST 22, 2022
Even with ransomware costing billions of dollars in losses and cyber insurance claims, organizations are still impacted beyond the checkbook. Cyber insurance has become more critical to organizations to help offset the risk to the company. Maintaining these critical resources directly impacts the organization’s risk scoring.

Security Boulevard
SEPTEMBER 1, 2021
tag=Ransomware'>Ransomware</a> <a href='/blog?tag=Cyber-attacks'>Cyber-attacks</a> In the business and technology world, perhaps its main effect has been to press the accelerator on digital transformation in organizations across the globe. The evolving cyber threat landscape.

Thales Cloud Protection & Licensing
JUNE 6, 2018
Gartner defines digital risk management as “the integrated management of risks associated with digital business components, such as cloud, mobile, social, big data, third-party technology providers, OT and the IoT.” Ransomware. Best Practices for Digital Risk Management. Interested in learning more?

SC Magazine
MAY 28, 2021
Some saw this as a typical ransomware attack, albeit on a vulnerable target. That distinction is important for identifying risk. So we have to be a little pragmatic also when it comes to drawing boundaries… as digital transformation takes over OT, OT and IT get closer together.”

The Last Watchdog
MARCH 11, 2020
Speed is what digital transformation is all about. Teeming threat landscape Security leaders’ key priority is reducing exposures to the cyber risks they know are multiplying. The number of such attacks appears to be relatively low, but they can do substantial damage; at the moment, ransomware extortion often is the end game.

Security Boulevard
FEBRUARY 3, 2021
There was a widespread lack of awareness of cybersecurity, with almost half of respondents having either not heard of, or not knowing what ransomware is. If an employee can at least recognise a malicious email, then they will be far less likely to click on a link or open a file or image containing ransomware.

Herjavec Group
OCTOBER 1, 2021
It’s been wild to see the digital transformations happening across all industries over the past few years but think about the progressions when it comes to social media. Enterprises and organizations are not the only ones at risk when it comes to cyber-attacks, and that’s a mentality we need to emphasize.

Security Boulevard
OCTOBER 10, 2022
How did ransomware propagate across several VLANs protected with micro-segmentation and isolation? With over 1000 plus vendors going to great lengths to show their greatest over their competitors, the consuming enterprise CISO and CIO will continue to breach, data exfiltration, and ransomware. Something failed!

IT Security Guru
AUGUST 16, 2021
In May the US Colonial Pipeline shut its operational network after a ransomware cyber-attack. Not to have a solid security strategy is also at odds with the business and digital transformation strategies that companies are embarking on. It’s said to be one of the costliest attacks for an economy.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content