Multiple flaws in Teltonika industrial cellular router expose OT networks to hack
Security Affairs
MAY 16, 2023
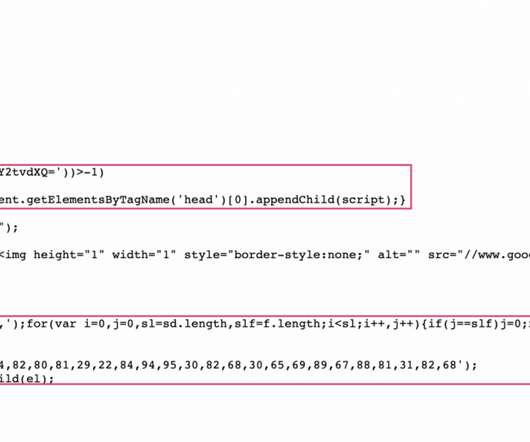
Teltonika Networks is a leading manufacturer of networking solutions, widely adopted in industrial environments, including gateways, LTE routers, and modems. The study focuses on the RUT241 and RUT955 cellular routers manufactured by Teltonika, and on the Remote Management System (RMS) provided by the vendor.














Let's personalize your content