Cyberpunk 2077 Headaches Grow: New Spyware Found in Fake Android Download
Threatpost
DECEMBER 18, 2020
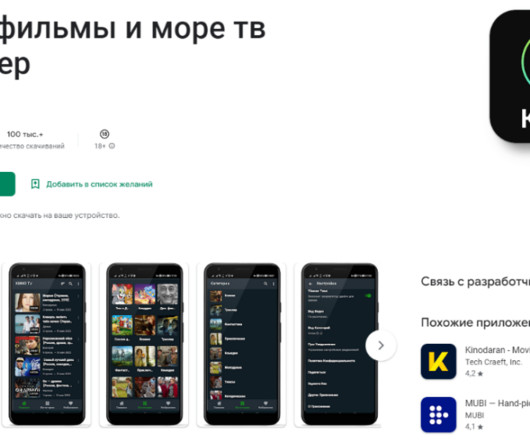
Threat actors impersonate Google Play store in scam as Sony pulls the game off the PlayStation store due to myriad performance issues.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Threatpost
DECEMBER 18, 2020
Threat actors impersonate Google Play store in scam as Sony pulls the game off the PlayStation store due to myriad performance issues.
Security Affairs
MARCH 8, 2020
Experts uncovered a new Coronavirus (COVID-19 ) -themed campaign that is distributing a malware downloader that delivers the FormBook information-stealing Trojan. Experts at MalwareHunterTeam uncovered a new malspam campaign exploiting the fear in the Coronavirus (COVID-19) to deliver malware.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Identity IQ
APRIL 29, 2021
What is Malware? . Malware is an umbrella term used to describe any malicious software designed to harm, exploit, or extract sensitive data from a system, device, or network. Why do Cybercriminals Use Malware? How does Malware Spread? Types of Malware. Warning Signs Cour computer Is Infected by Malware.

SecureList
MARCH 1, 2021
The word “covid” in various combinations was typically used in the names of packages hiding spyware and banking Trojans, adware or Trojan droppers. The mobile malware Trojan-Ransom.AndroidOS.Agent.aq Number of attacks on mobile users in 2019 and 2020 ( download ). apk , tousanticovid.apk , covidMappia_v1.0.3.apk

SecureWorld News
MARCH 29, 2024
Malvertising acts as a vessel for malware propagation. To set such a stratagem in motion, cybercriminals poison legitimate websites with ads that lead to shady URLs or download malicious code camouflaged as something harmless. One of the biggest pitfalls with malvertising is how difficult it can be to detect.

Identity IQ
FEBRUARY 21, 2023
Most times, spam emails contain malware , which can compromise your devices connected to the email. Trojan Horses A trojan horse is a malware that is disguised to appear as a legitimate program. However, when you download or click on the attachment, your device becomes infected. It is easy to fall victim to a trojan horse.
SecureList
AUGUST 30, 2023
Quarterly figures According to Kaspersky Security Network, in Q2 2023: A total of 5,704,599 mobile malware, adware, and riskware attacks were blocked. Quarterly highlights The number of malware, adware, or unwanted software attacks on mobile devices began to climb again in Q2 2023. of all threats detected.

Webroot
OCTOBER 25, 2021
In 2020, phishing scams spiked by 510 percent between January and February alone. To combat phishing scams, it helps to have filters that can proactively alert users if there’s a high chance that a form field or website is likely to steal credentials. Web-borne malware remains widespread. Fake apps are still cause for concern.
SecureList
MAY 27, 2022
According to Kaspersky Security Network, in Q1 2022: 6,463,414 mobile malware, adware and riskware attacks were blocked. Number of attacks targeting users of Kaspersky mobile solutions, Q1 2020 — Q1 2022 ( download ). These types of apps occupy seven out of the twenty places in our malware ranking for Q1. Quarterly figures.

eSecurity Planet
JUNE 16, 2022
billion malware attacks were identified by the report. Cisco Umbrella , analyzing the threat environment for 2022, found that 86% of organizations experienced phishing, 69% experienced unsolicited crypto mining, 50% were affected by ransomware, and 48% experienced some form of information-stealing malware. Crimeware and spyware.

Hot for Security
JUNE 14, 2021
Most security threats faced by regular users arrive via the Internet, whether it’s a malicious app or a rigged website , a scam delivered through the user’s social media channels, or a phishing scheme carried out via email or SMS. In many cases, no malware is needed to compromise this data. Platform-agnostic threats. Weaponizing hype.

SecureList
NOVEMBER 26, 2021
According to Kaspersky Security Network, in Q3 2021: 9,599,519 malware, adware and riskware attacks on mobile devices were prevented. We have seen no new mass campaigns seeking to distribute any specific mobile malware family; nor were there any newsworthy events similar to what we had early into the COVID-19 pandemic. Verdict. %*.

Malwarebytes
OCTOBER 26, 2021
We talked to members of our Malware Removal Support team and asked them what kind of problems they get asked to solve for our customers. Some people get so convinced they have spyware on their system that they contact our support team to help them get rid of it. Social media and scams. More Facebook concerns.

Identity IQ
FEBRUARY 18, 2021
App downloads. If a “Not Secure” warning appears on your browser when you visit a website, it is not necessarily affected by malware. Malware is any type of software or program designed to harm a computer, steal data or hold victims to ransom such as a computer virus, Trojan horse, ransomware, spyware, wiper, worm or adware.

IT Security Guru
FEBRUARY 13, 2023
With so many well known banking sites falling short when it comes to blocking fraudsters, cybersecurity experts at VPNOverview have compiled a list of 12 safety tips to keep your money safe from malware and phishing scams. What are the possible dangers of online banking? Do not download any files they may contain. 7.

SecureList
NOVEMBER 22, 2022
Unlike common stealers, this malware gathered data that can be used to identify the victims, such as browsing histories, social networking account IDs and Wi-Fi networks. According to the freshest data on DeFi, every hour 15 newly deployed scams against smart contracts are detected. million downloads.

Hot for Security
JUNE 15, 2021
Given the portability and myriad of functionalities, mobile devices are highly susceptible to cyber threats, including malware, spyware and phishing attempts that may compromise that precious piece of tech we keep in our pocket and any information stored on it. Security at home or on the go.

SecureList
FEBRUARY 16, 2023
Thus, during the World Cup a brand-new scam appeared: it offered users to win a newly released iPhone 14 for predicting match outcomes. In a typical internet hoax manner, crypto scam sites offered visitors to get rich quick by paying a small fee. “Promotional campaigns by major banks” were a popular bait in 2022.

Security Affairs
APRIL 24, 2022
Please vote for Security Affairs as the best European Cybersecurity Blogger Awards 2022 – VOTE FOR YOUR WINNERS Vote for me in the sections “The Underdogs – Best Personal (non-commercial) Security Blog” and “The Tech Whizz – Best Technical Blog” and others of your choice.

Malwarebytes
FEBRUARY 6, 2023
The pop up blocker in particular was a big help with the proliferation of adware and spyware plugging into advertising networks. To put this into some way-back-when context: If you were caught out by a malware attack which pushed 8 whole megabytes at you , this was treated as a cavalcade of malware. Exploits were rampant.
SecureList
FEBRUARY 15, 2021
Agentb malware family. The Kaspersky Anti-Phishing component blocked 434,898,635 attempts at accessing scam sites. In most cases, scammers, as before, claimed to have used spyware to film the blackmail victim watching adult videos. When the recipient tried to open these, malware was loaded onto the computer.

SecureList
MARCH 15, 2021
In 2020, criminals launched a variety of scams that exploited the pandemic topic from just about every angle, from advertisements to masks when they were in short supply to special refunds from the government. However, upon clicking the attachment, the users would download Trojans ranging from spyware to backdoors.

SiteLock
AUGUST 27, 2021
Cyberattacks are often caused by malware, which is the umbrella term used to describe software created for malicious purposes. You may be most familiar with computer malware such as Trojan viruses and spyware, which can be used to retrieve sensitive data from a computer or even take control of the system.
SecureList
FEBRUARY 9, 2022
The most common malware family found in attachments were Agensla Trojans. The same outcome was observed when users tried to download or stream sports events or other content, the only difference was visitors might not be able to watch anything without registering. In 2021: 56% of e-mails were spam.

Digital Shadows
NOVEMBER 10, 2022
Scams could present themselves in many forms. For instance, financially-motivated threat actors often plant in malicious URLs spoofing these events to fraudulent sites, hoping to maximize their chances of scamming naive internet users for a quick (illicit) profit.

Malwarebytes
MAY 10, 2023
(Verizon Mobile Security Index 2022) 9 percent of organizations suffered a mobile malware attack in 2022. In this post, we’ll delve into mobile malware trends, gather critical insights, and anticipate future scenarios to prepare MSPs for the complex landscape of mobile malware.

SecureList
FEBRUARY 21, 2022
But it is too early to celebrate: attacks are becoming more sophisticated in terms of both malware functionality and vectors. Experts also continued to find malware in apps on Google Play, despite Google’s efforts to keep threats off the platform. Number of detected malicious installation packages, 2018–2021 ( download ).

Spinone
NOVEMBER 1, 2019
DLP is included in the organization policy, but individuals must also use this strategy to keep all data safe during ransomware or malware attack. Malware and Ransomware Adware – Software that automatically displays or downloads material when a user is offline. The most widespread spyware are keyloggers and trojans.

CyberSecurity Insiders
JANUARY 31, 2021
Regardless of how familiar you are with Information Security, you’ve probably come across the term ‘malware’ countless times. From accessing your business-critical resources and sensitive information to halting business operations and services, a malware infection can quickly become an organization’s worst nightmare come true.

eSecurity Planet
SEPTEMBER 29, 2021
Recent research by Positive Technologies looked at the cyber threat landscape during Q2 2021 and found that ransomware attacks reached “stratospheric” levels, accounting for 69% of all malware attacks, a huge jump from 39% in Q2 2020. Detect compromised accounts, insider threats, and malware. EnigmaSoft.

SecureList
AUGUST 5, 2021
In addition to various cloud-related emails, we blocked messages disguised as business correspondence and containing links to malware. pdf.exe) that the victim was asked to download was a malicious program known as Backdoor.Win32.RWS.a. Parcel scam: buy one, get none. Therefore, any offer to buy them is evidently a scam.

Security Boulevard
JANUARY 25, 2022
A Compilation of Currently Active Full Offline Copies of Cybercrime-Friendly Forum Communities – Direct Technical Collection Download -[RAR]. A Compilation of Personally Identifiable Information on Various Iran-based Hacker Groups and Lone Hacker Teams – Direct Technical Collection Download – [RAR].

Webroot
MAY 12, 2021
However, when examined more closely, most hosting IPs were found to have hosted malicious content (such as some serious malware ) in the past, and had connections to other high-risk IPs. Contextual graphs such as these show the relationships between web hosts and dropped malware. Bitcoin scams. For instance, rojadirecta[.]me

Malwarebytes
AUGUST 9, 2022
This threat is flagged when malware modifies a registry setting that changes the default Windows debugger to a malware executable. Beyond spikes in detections, the education sector has dealt with an onslaught of attacks ranging from spyware and denial of service tools to ransomware. Wisconsin, and Illinois.

SecureList
NOVEMBER 1, 2021
Scamming championship: sports-related fraud. Scam: get it yourself, share with friends. Note too that QR codes from questionable sources can carry other threats, for example, spreading malware or debiting money in favor of the scammers. Even in official mobile app stores, malware can sometimes sneak in.

SecureList
NOVEMBER 10, 2021
With millions of new users on streaming platforms, cyberattackers have recognized this heightened demand and seek to take advantage of it by distributing streaming phishing scams and spreading malware under the guise of users’ favorite shows. Malware and riskware instead of streaming. Methodology. Apple TV Plus.
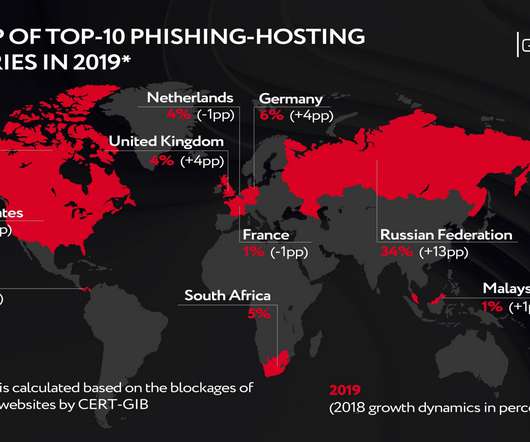
Security Affairs
MAY 8, 2020
Thus, the number of phishing attacks on cloud storages nearly doubled last year, while Internet providers have seen the three-fold increase in the number of phishing scams targeting them. Malware delivery: what’s on the menu? CERT-GIB’s findings indicate that phishing attack perpetrators have revised their so-called target pool.

SecureList
MAY 3, 2021
In Q1 2021, new banking scams appeared alongside ones that are more traditional. In actual fact, scanning the code resulted in a data leak, money theft or device infection, if it contained a link to a web page with malware. Proportion of spam in global email traffic, Q4 2020 and Q1 2021 ( download ). Malware families.

Security Affairs
JULY 7, 2019
ViceLeaker Android spyware targets users in the Middle East. Updates for Samsung, the scam app with 10M+ downloads. Cryptomining Campaign involves Golang malware to target Linux servers. FBI warns on sextortion scams targeting teenagers. Godlua backdoor, the first malware that abuses the DNS over HTTPS (DoH).

SecureList
MARCH 7, 2024
Some of the scam sites discovered promised to reimburse a certain sum to the customers of a major international telecommunications company. Alongside the usual get-rich-doing-nothing and paid survey scams, we encountered a few less conventional scenarios. Scam sites also used cryptocurrency as bait.

SC Magazine
APRIL 6, 2021
The backdoor, which is sold as a malware-as-a-service offering to affiliate cybercriminal entities including the infamous FIN6, Cobalt Group and Evilnum groups, comes packaged in a malicious zip file with a file name that includes the exact job position that’s listed on the individual target’s LinkedIn profile. edu,’ said the IRS release.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content