ICE Is a Domestic Surveillance Agency
Schneier on Security
MAY 11, 2022
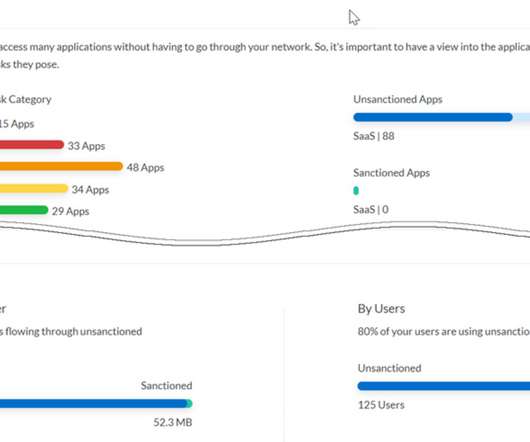
Georgetown has a new report on the highly secretive bulk surveillance activities of ICE in the US: When you think about government surveillance in the United States, you likely think of the National Security Agency or the FBI. You might even think of a powerful police agency, such as the New York Police Department. But unless you or someone you love has been targeted for deportation, you probably don’t immediately think of Immigration and Customs Enforcement (ICE).







































Let's personalize your content