LapDogs: China-nexus hackers Hijack 1,000+ SOHO devices for espionage
Security Affairs
JUNE 28, 2025
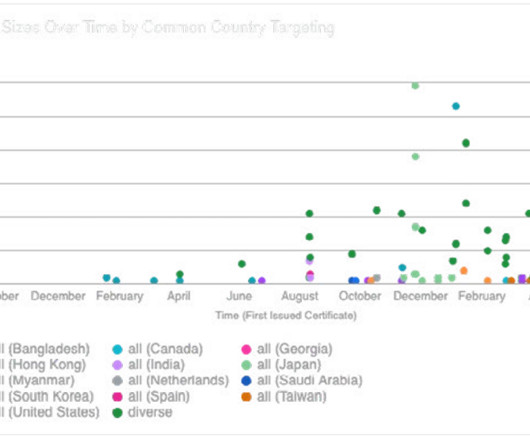
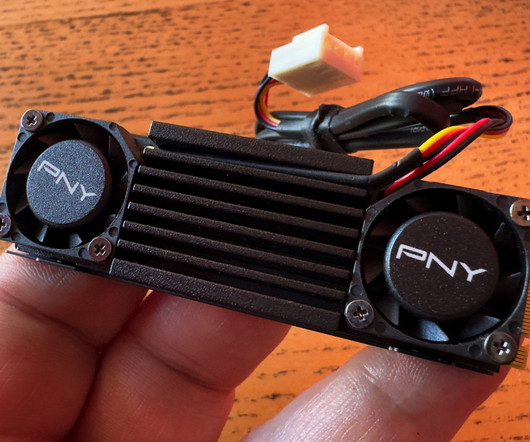
Over 1,000 SOHO devices were hacked in a China-linked spying campaign called LapDogs, forming a covert network to support cyber espionage. Security researchers at SecurityScorecard’s STRIKE team have uncovered a cyber espionage campaign, dubbed LapDogs, involving over 1,000 hacked SOHO (small office/home office) devices. These compromised devices formed a hidden network, called an Operational Relay Box (ORB), used to support long-term spying operations linked to China-nexus hacking groups.





































Let's personalize your content