Australia Threatens to Force Companies to Break Encryption
Schneier on Security
SEPTEMBER 9, 2024
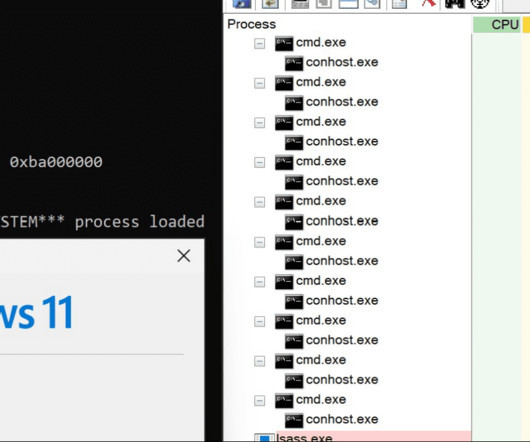
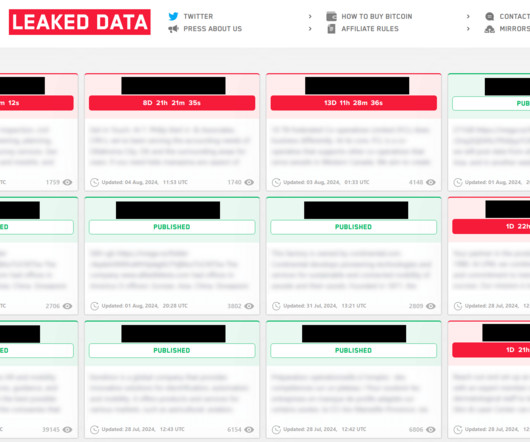
In 2018, Australia passed the Assistance and Access Act, which—among other things—gave the government the power to force companies to break their own encryption. The Assistance and Access Act includes key components that outline investigatory powers between government and industry. These components include: Technical Assistance Requests (TARs): TARs are voluntary requests for assistance accessing encrypted data from law enforcement to teleco and technology companies.























Let's personalize your content