Can Security Experts Leverage Generative AI Without Prompt Engineering Skills?
Tech Republic Security
OCTOBER 22, 2024
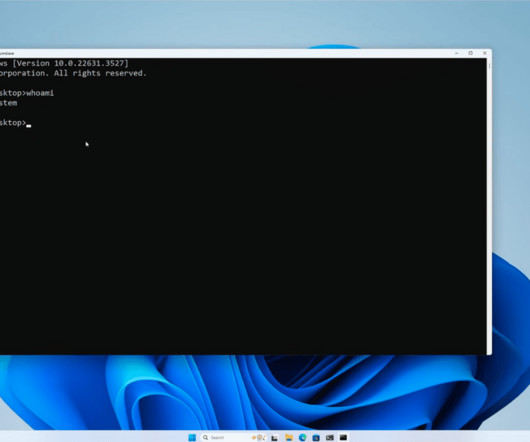
A study at Rensselaer Polytechnic Institute presented at ISC2 Security Congress compared ChatGPT-written training prompted by security experts and prompt engineers.















Let's personalize your content