Introducing next-generation firewall from Palo Alto Networks to support 5G-enabled IoT, OT and IT use cases
CyberSecurity Insiders
JANUARY 11, 2022
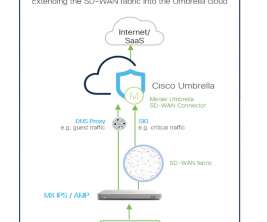
Next-generation firewalls from Palo Alto Networks with AT&T Multi-Access Edge Computing (MEC) solutions are designed to help protect enterprises while optimizing security performance for these new use cases. They also help reduce complexity by assisting the customer with ongoing configuration changes to their firewall policies.
















































Let's personalize your content