Millions of Xiongmai video surveillance devices can be easily hacked via cloud feature
Security Affairs
OCTOBER 10, 2018
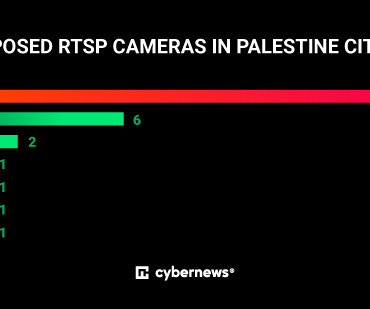
Millions of Xiongmai video surveillance devices can be easily hacked via cloud feature, a gift for APT groups and cyber crime syndicates. The flaws reside in a feature named the “XMEye P2P Cloud” that is enabled by default which is used to connect surveillance devices to the cloud infrastructure. Who controls these servers?
















Let's personalize your content