GUEST ESSAY: Securely managing access controls is vital to preserving the privacy of healthcare data
The Last Watchdog
NOVEMBER 8, 2021
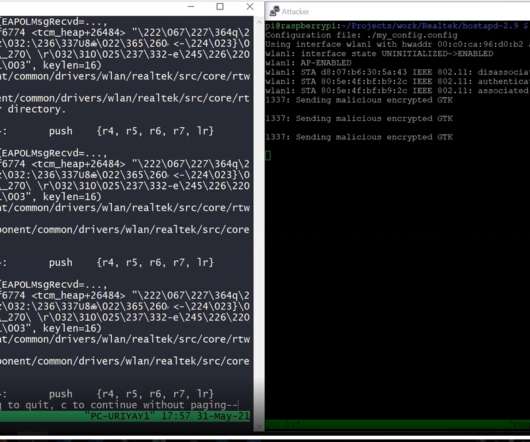
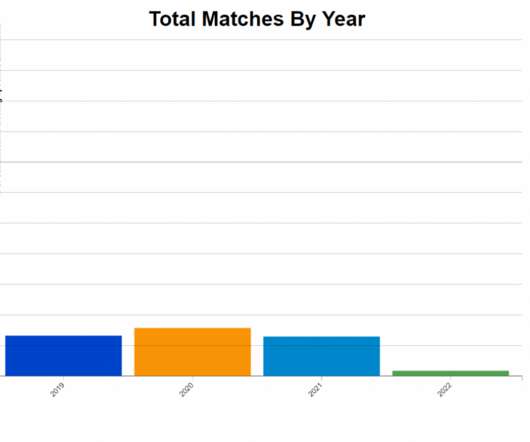
There’s no doubt, the increasing use of telemedicine, the explosion of health-based cloud apps, and innovative medical IoT devices are improving the patient care experience. Related: Hackers relentlessly target healthcare providers. There are many reasons for the vulnerable state of healthcare data. Patient data exposures.














































Let's personalize your content