GUEST ESSAY: Here’s why castle-wall defenses utterly fail at stopping deceptive adversaries
The Last Watchdog
OCTOBER 25, 2021
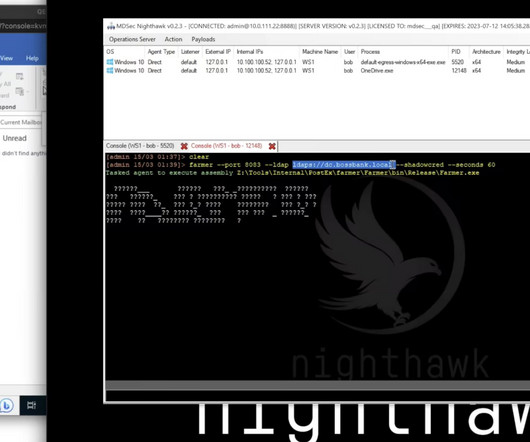
There are several methods of active defense that companies can utilize to safeguard their networks, and it’s time for CISOs to start picking. Traditional network security solutions, such as firewalls, are not effective at detecting and stopping lateral attack movement – and that’s where the real damage is done.















Let's personalize your content