Flaws in firmware expose almost any modern PC to Cold Boot Attacks
Security Affairs
SEPTEMBER 13, 2018
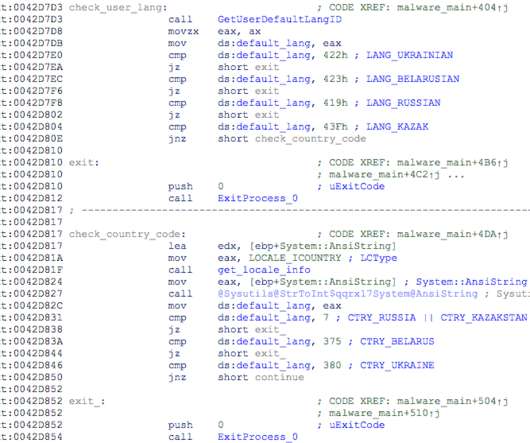
New Firmware Flaws Resurrect Cold Boot Attacks. A team of security researchers demonstrated that the firmware running on nearly all modern computers is vulnerable to cold boot attacks. encryption keys, passwords) from a running operating system after using a cold reboot to restart the machine. Pierluigi Paganini.











































Let's personalize your content