How Password Managers Can Get Hacked
Dark Reading
APRIL 11, 2023
Password managers aren't foolproof, but they do help mitigate risks from weak credentials and password reuse. Following best practices can contribute to a company's defenses.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Dark Reading
APRIL 11, 2023
Password managers aren't foolproof, but they do help mitigate risks from weak credentials and password reuse. Following best practices can contribute to a company's defenses.

eSecurity Planet
MARCH 8, 2022
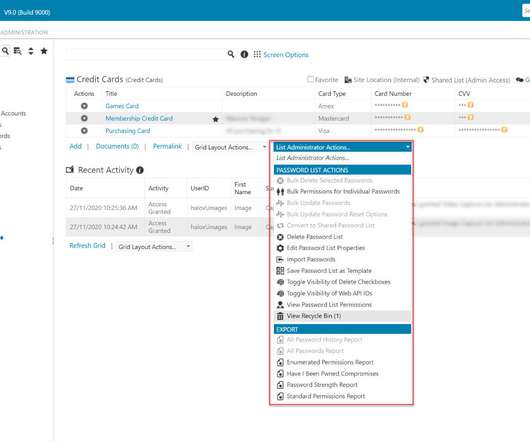
The average internet user has somewhere around 100 accounts, according to NordPass research, meaning they have to track 100 different passwords or risk using the same one over and over. Users can share password files securely with encrypted transmissions. Vault health reports Directory sync Secure password sharing.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Graham Cluley
JANUARY 3, 2023
Do you use the LastPass password manager? Did you know they suffered a data breach, and that your passwords may be at risk? You do now. Here's what you need to know.

Security Boulevard
FEBRUARY 27, 2023
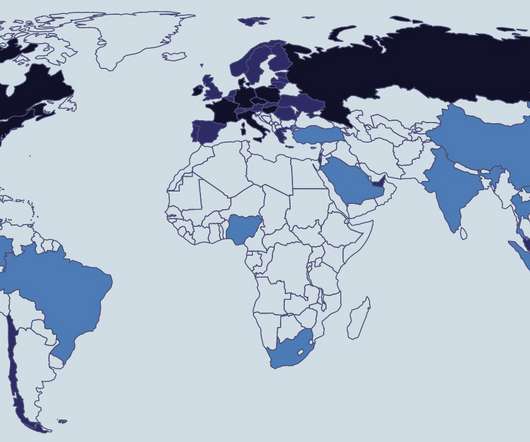
In recent months, the password manager industry has taken a significant cyber hit. In December 2022, one of the world’s most popular password managers, LastPass, notified its customers of a massive breach that exposed customer data and put their password vaults at risk if weak passwords were used.
SC Magazine
APRIL 23, 2021
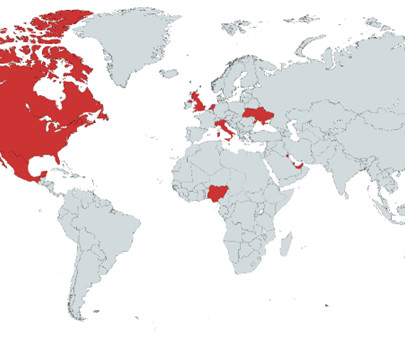
Researchers at CSIS Security Group claim they have discovered what they think might be the next big supply chain hack. If customers were compromised, it follows a wave of other damaging software supply chain hacks discovered in the last four months. This is a developing story. Check back for updates.

Identity IQ
MAY 13, 2024
What Are the Risks of a Data Breach? IdentityIQ In a society dominated by digital interconnectedness, the risks associated with data breaches loom over individuals, businesses, and society at large. The ramifications extend past financial losses due to personal, corporate, and regulatory privacy being at risk.

The Security Ledger
JANUARY 2, 2019
Customers who use the Blur secure password manager by Abine may have had sensitive information leaked, according to a statement by Abine, the company that makes the product. . The post Abine says Blur Password Manager User Information Exposed appeared first on The Security Ledger.

Krebs on Security
AUGUST 5, 2019
Crooks are constantly probing bank Web sites for customer accounts protected by weak or recycled passwords. Most often, the attacker will use lists of email addresses and passwords stolen en masse from hacked sites and then try those same credentials to see if they permit online access to accounts at a range of banks.

Security Affairs
SEPTEMBER 23, 2022
According to Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities , FCEB agencies have to address the identified vulnerabilities by the due date to protect their networks against attacks exploiting the flaws in the catalog. SecurityAffairs – hacking, Zoho). Pierluigi Paganini.

The Last Watchdog
MAY 2, 2019
While the internet and social media have been very positive for businesses, there remains an inherent risk when it comes to how brands manage their Facebook, Twitter, and Instagram accounts. 1 : Cybercrime Businesses should always be very aware of the threat of cybercriminals, and social media also poses very real cyber-security risks.

The Last Watchdog
MARCH 6, 2021
Related: Poll confirms rise of Covid 19-related hacks. Passwords for accounts should be unique for every account and should compromise a long string of distinct characters, lower and upper case letters, and numbers. It is difficult to remember all passwords. Even the most strong password is not enough.

Troy Hunt
NOVEMBER 7, 2018
It's just another day on the internet when the news is full of headlines about accounts being hacked. This is when hackers try usernames and password combos leaked in data breaches at other companies, hoping that some users might have reused usernames and passwords across services.

Identity IQ
JANUARY 16, 2023
Criminal hackers attempted to break into Norton LifeLock customer accounts and possible password managers, meaning they might have gained access to customers’ usernames, passwords and other personal information. To keep your online identity safe, it is important to use strong and unique passwords for each of your accounts.

Approachable Cyber Threats
MAY 30, 2023
Category Awareness, Cybersecurity Fundamentals, Physical Security Risk Level You may have thought that hackers wore black suits and rappelled off the roof to hack a company, but that only exists in Hollywood. This incident would be considered a "data breach," and it's the potential consequence of poor Access Control management.

Security Affairs
DECEMBER 1, 2022
Eliminating the risk of a data breach is nearly impossible, but some things can be done to reduce it significantly. While no plaintext passwords or financial data was stolen, the hack did expose answers to security questions. All of that could’ve been avoided had SolarWinds implemented a strong password policy.

Hot for Security
JUNE 8, 2021
The most extensive data leak collection to date, dubbed ‘RockYou2021’, was dumped on popular hacking forums earlier this month. billion password entries, presumably obtained from previous data leaks and breaches. What are the risks? According to a CyberNews report , a forum user posted a 100GB text file with 8.4

SecureWorld News
APRIL 2, 2024
Assuming this information is from the previous hack (2021), hopefully, AT&T has already implemented remediation." The risks stemming from such a massive Personal Identifiable Information (PII) exposure are severe according to Anne Cutler, Cybersecurity Evangelist at Keeper Security.

Malwarebytes
APRIL 16, 2024
million records to a hacker forum, claiming they originated from a March 2024 hack at Canadian retail chain Giant Tiger. In March, one of Giant Tiger‘s vendors, a company used to manage customer communications and engagement, suffered a cyberattack, which impacted Giant Tiger, as reported by CBC. Change your password.

Identity IQ
JULY 17, 2023
Cybercriminals can exploit stolen usernames and passwords to gain unauthorized access to your accounts, compromising your personal and financial information. It’s vital to prioritize the protection of your digital identity to mitigate these risks and maintain your online security.

Identity IQ
JULY 17, 2023
Cybercriminals can exploit stolen usernames and passwords to gain unauthorized access to your accounts, compromising your personal and financial information. It’s vital to prioritize the protection of your digital identity to mitigate these risks and maintain your online security.

Schneier on Security
DECEMBER 4, 2018
To remain anonymous and secure on the Internet, invest in a Virtual Private Network account, but remember, the bad guys are very smart, so by the time this column runs, they may have figured out a way to hack into a VPN. I get that unsecured Wi-Fi is a risk, but does anyone actually follow this advice? Yes to the first part.

Approachable Cyber Threats
SEPTEMBER 30, 2021
Category Cybersecurity Fundamentals Risk Level. You just heard in the news about another online company getting hacked and all of their password’s getting stolen; including yours. It could mean that even though it was an online retailer who got hacked, your bank account could ultimately be emptied.

Identity IQ
MAY 15, 2021
As important as they are, however, about 52 percent of people still use the same passwords across multiple accounts and 24 percent use a variation of common passwords that are easy to hack. Hackers employ different strategies to steal your passwords. To make this easier on yourself, consider using a password manager.

Security Affairs
MARCH 13, 2023
Recently, the password management software firm disclosed a “second attack,” a threat actor used data stolen from the August security breach and combined it with information available from a third-party data breach. .” The company addressed the vulnerability with the release of Plex Media Server 1.19.3 in May 2020.

Malwarebytes
DECEMBER 19, 2023
In a data breach notification , the company didn’t say what type of cyberattack caused the compromise of customer data, calling it a rather non-descriptive “External system breach (hacking).” Change your password. You can make a stolen password useless to thieves by changing it. Enable two-factor authentication.

CyberSecurity Insiders
NOVEMBER 17, 2021
An annual report released by NordPass states that online users are repeatedly committing the same mistake by using their own name as a password, which could put their online identity at a major risk in coming years. The post Cyber Threat by using own name as Password appeared first on Cybersecurity Insiders.

Krebs on Security
JANUARY 30, 2024
Sources close to the investigation tell KrebsOnSecurity the accused was a key member of a criminal hacking group blamed for a string of cyber intrusions at major U.S. Multiple security firms soon assigned the hacking group the nickname “ Scattered Spider.” 9, 2024, U.S. technology companies during the summer of 2022.

Approachable Cyber Threats
SEPTEMBER 30, 2021
Category Cybersecurity Fundamentals Risk Level. So you’ve spent the past few days starting to get your passwords updated and into your password manager. Those long, complex, unique passwords you’re setting are only one part of the equation to protecting your information. That’s a great start!

Security Affairs
NOVEMBER 25, 2020
SecurityAffairs – hacking, Data breach). “Retailers must take meaningful steps to protect consumers’ credit and debit card information from theft when they shop,” said Massachusetts AG Maura Healey. ” . . Pierluigi Paganini. The post Retail giant Home Depot agrees to a $17.5
Security Affairs
NOVEMBER 20, 2021
The annual study on top-used passwords published by Nordpass revealed that we are still using weak credentials that expose us to serious risks. Nordpass has published its annual report, titled “Top 200 most common passwords,” on the use of passwords. The report shows that we are still using weak passwords.
Security Affairs
FEBRUARY 24, 2023
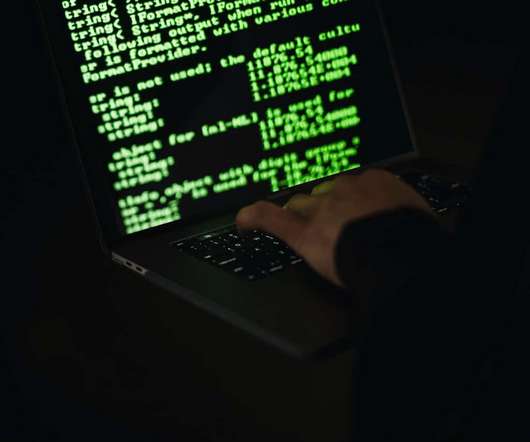
The issue affects tens of products, including Access Manager Plus, ADManager Plus, Password Manager Pro, Remote Access Plus, and Remote Monitoring and Management (RMM). The root cause of the problem is that ManageEngine products use an outdated third-party dependency, Apache Santuario.

Malwarebytes
OCTOBER 15, 2023
According to BleepingComputer , a cybercriminal claiming responsibility for the attack is selling the stolen database on a well-known hacking forum. Change your password. You can make a stolen password useless to thieves by changing it. Choose a strong password that you don't use for anything else.
eSecurity Planet
AUGUST 19, 2022
While it may sound pretty inconvenient, password managers can remove the hassle of typing your credentials, because you will have to reauthenticate sessions. See the Best Password Management Software & Tools. Cookies from the Developer’s Perspective. Such cookies must have a short expiration date.

SecureWorld News
SEPTEMBER 27, 2021
Hacker found weak link in port's password management software. In coverage by CNN , it was reported that the hackers were able to breach the web server by finding a vulnerability through password management software, ManageEngine ADSelfService Plus. "In UTC on August 19, according to the Coast Guard report.

Security Affairs
SEPTEMBER 7, 2022
As virtually every aspect of day-to-day life and business is conducted online, the added convenience has also brought added risk. Cybercriminals continue to evolve their tactics to exploit vulnerabilities, consistently developing new means to execute DDoS attacks, hacks, and fraud for financial gain or sabotage.

SiteLock
AUGUST 27, 2021
One year ago in February, the major eBay hack was in progress, eventually resulting in over 233 million passwords being stolen. 2015 Cyber Security Risks. TechRadar recently posted an article covering the top seven cyber security risks that businesses should be aware of for 2015. Anthem Cyber Attack.

Approachable Cyber Threats
MAY 30, 2023
Category Awareness, Cybersecurity Fundamentals, Physical Security Risk Level You may have thought that hackers wore black suits and rappelled off the roof to hack a company, but that only exists in Hollywood. This incident would be considered a "data breach," and it's the potential consequence of poor Access Control management.

Webroot
NOVEMBER 29, 2022
It’s a dirty truth that big businesses suffer data breaches – that means the longer you use a password the more likely it’s been hacked. Even if you’re not using that old website, hackers might know your information and will try logging in to common sites using your old email + password combination. Visit reputable sites.

Identity IQ
MAY 2, 2023
What are the Benefits of a Password Manager? IdentityIQ Passwords are essential when keeping your information safe on your devices. But unfortunately, many people use weak or the same password, making it easy for hackers to crack them. Research shows that 52% of people reuse passwords for multiple accounts.

Security Affairs
MAY 2, 2021
SecurityAffairs – hacking, Mac OS zero-day). Every week the best security articles from Security Affairs free for you in your email box. Every week the best security articles from Security Affairs free for you in your email box. If you want to receive the weekly Security Affairs Newsletter for free subscribe here. Pierluigi Paganini.

CyberSecurity Insiders
NOVEMBER 14, 2021
These are examples of weak passwords that will put your accounts at risk. We know it’s difficult to remember complex, meaningless passwords, which is why specialists use password managers. This way, you only have to remember one password that keeps the rest safe. . #3: 3: Two-Factor Authentication (2FA).

CyberSecurity Insiders
DECEMBER 20, 2021
Their distributed nature means someone would have to hack the whole network , not just a few devices, to infiltrate them. That level of security would help maintain the benefits of remote monitoring and tracking without introducing more risks. Blockchains also have security advantages over alternative systems. Train Employees.

eSecurity Planet
SEPTEMBER 24, 2021
If you’re looking for a password manager for your business, Bitwarden and LastPass might be on your list of potential solutions. Both vendors will help you and your employees store access credentials, improve password health, and share sensitive information securely. PBKDF2 SHA-256 encryption for master passwords.

CyberSecurity Insiders
DECEMBER 6, 2022
To avoid these risks, companies need to develop a culture of cybersecurity that will lead to sustainable behavioral change whether employees are in the office or not. 2 – The proliferation of attack vectors will put companies at risk. Companies should also provide clear channels for reporting suspicious incidents.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content