New PumaBot targets Linux IoT surveillance devices
Security Affairs
MAY 28, 2025
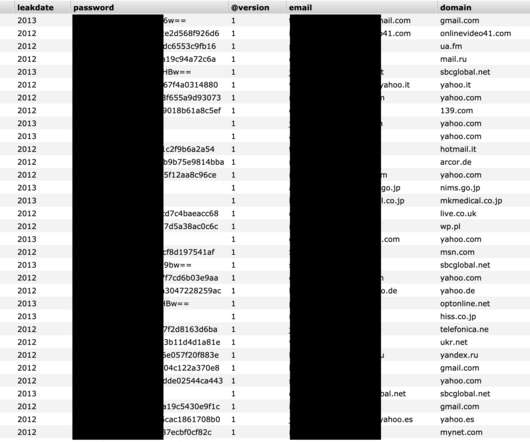
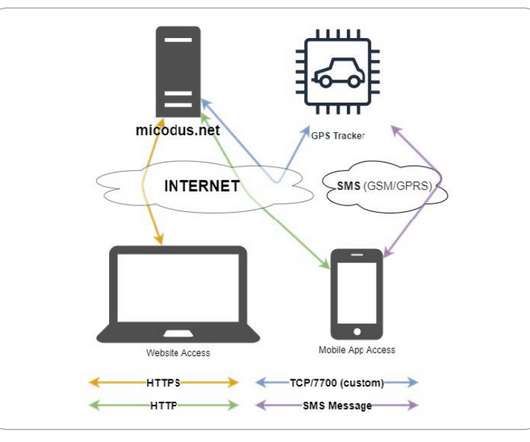
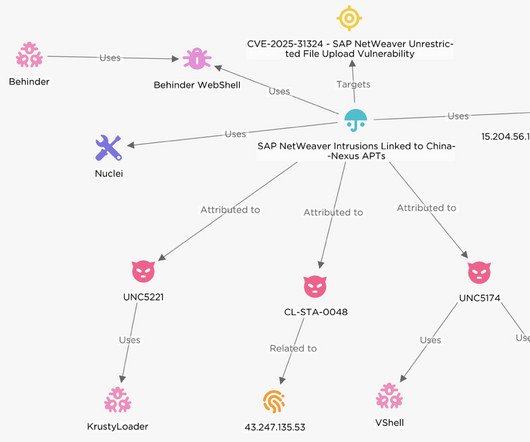
PumaBot targets Linux IoT devices, using SSH brute-force attacks to steal credentials, spread malware, and mine crypto. Darktrace researchers discovered a new botnet called PumaBot targets Linux-based IoT devices, using SSH brute-force attacks to steal credentials, spread malware, and mine cryptocurrency. ” states the report.



































Let's personalize your content