News Alert: Utimaco finds regional disparities in consumers’ level of trust in digital security
The Last Watchdog
JULY 10, 2023
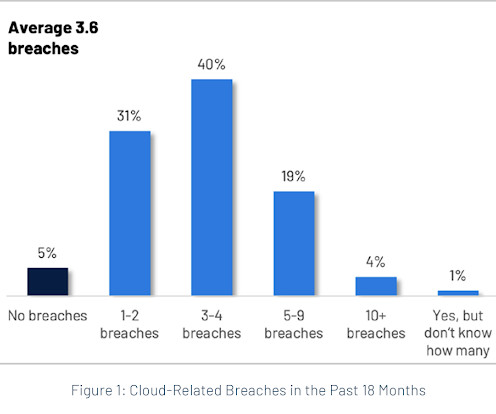
The research found a central contradiction of digital life: consumers were very enthusiastic about digital offerings, from connected vehicles to digital health services, but they were equally wary of security risks around these digital services. 36% of respondents have been the victim of data loss, identity theft or digital fraud. •41%



















Let's personalize your content